“Watering Hole” is a cyber attack strategy in which the victim is a particular group (organization, industry, or region). In this attack, the attacker typically observes which websites or applications the group often uses and infects one or more of them with malware. Eventually, some members of the targeted group become infected.
The method is typically used to target high-security targets through their low-security contacts, employees, business partners and connected personnel.
While the target will do its best to be careful while using their device and keep themselves protected, their messages and phone calls go to other devices, which might be unprotected and used in an unsafe way.
Known attacks are: 2018 Chinese state-level attack, 2017 ExPetr attack and the 2016 Polish banks attack.
There is no need for a precious zero day exploit, the use of professional first class hackers, or the collaboration with leading intelligence agencies to manage these attacks.
The attack can be perpetrated through utilizing raw access points, unsecured wireless networks, insecure or vulnerable websites, social engineering and other methods which are not state of the art in cyber attacks.
Here we analyze groups of Android applications installed while tricking users that were accessing targeted Android applications, news sites and liberal political issues journals around the Middle East.
Trojan RSS at the Watering Hole
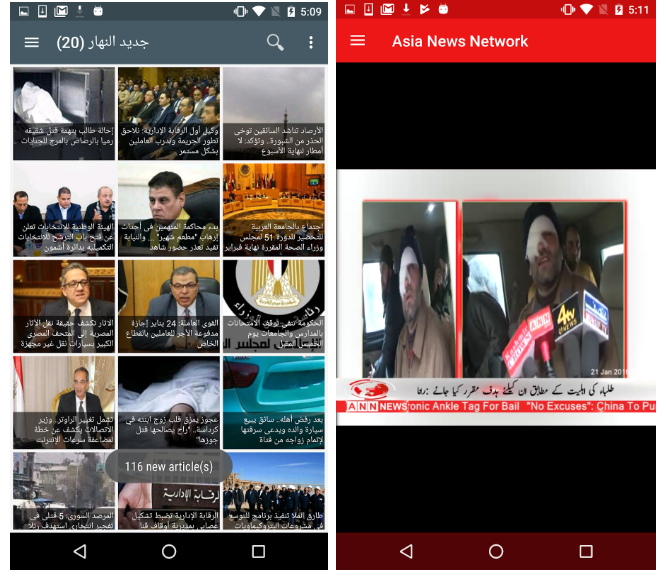
An innocent looking application with malicious spyware code payload is often called a Trojan Horse. One of the applications in our case study is ArabicRSS. It is the same as the legitimate application that could be safely downloaded and installed from the market, but with a malicious spyware code payload.
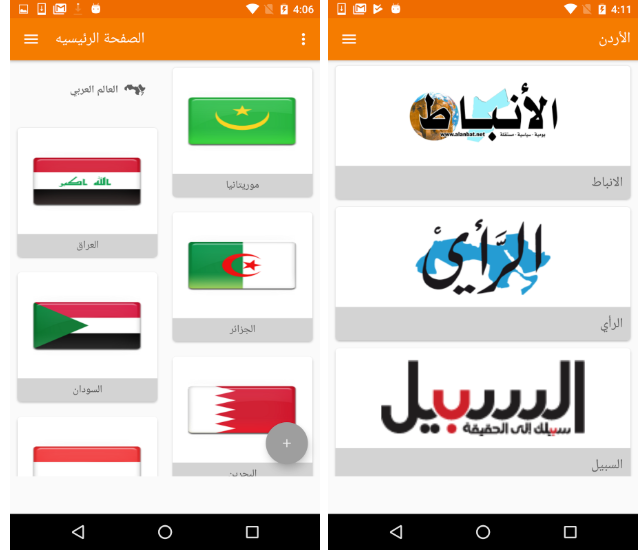
Al-Hayat (“The life”) is a London-based, pan-Arab newspaper and the preferred venue for liberal intellectuals who wish to express themselves to a large public. The watering hole victims in our case study are the Android device users who had an interest in several political issues at the time.
The attacks had been carried out by the redirection from the AL-Hayat and other related sites, and by other social engineering methods to a site tricking the user into downloading and installing the malicious Trojan.
Redirection from a legitimate source to a site on which the user will download the malware can be done by simple techniques such as a Man In The Middle Attack (MITM), Social Engineering and other redirection means. In addition, the attacker can use vulnerabilities in the websites and inject malicious JavaScript or HTML code redirecting the target to a separate site where the malware is hosted.
It is commonplace to decompile an application that can be legitimately downloaded from the app store, ‘inject’ malicious code payload that will work confidentially on the attacked device and repack the application’s APK(app file).
ArabicRSS.apk Application
Let us examine the ArabicRss.apk 3.4.1 trojan-infected application. The original ArabicRSS.apk application is a legitimate app for reading RSS feeds of several main Arabic language news sites.
The Trojan enables various spyware data-traffic driven functions of sending and monitoring: contacts, SMS messages, call logs, device location, device information, account details and images from the DCIM (Digital Camera IMages) directory.
Additional spyware functions include: location tracing, call recording, and regular surround recording – triggered by the screen being turned off.
Trojan payload code can be found in numerous open source projects. In the ArabicRSS case, the Trojan payload is based on reverse engineering of an older version of the commercial spyware, Spymaster Pro.
The application apparently looks and functions the same with or without the Trojan payload.

The Trojan Network
Trojan agent networks are usually managed by a Command and Control (C&C) server architecture.
The C&C responsibilities include collecting the data from the Trojan agent nodes and sending them commands for the different spying actions the Trojan is able to commit.
The ArabicRSS Trojan was one out of a group of at least five different applications that had the same Trojan payload. We mark them as the G2 group.
In total, there are at least three different Trojan payloads found at least at 13 different applications controlled from two different C&C servers.
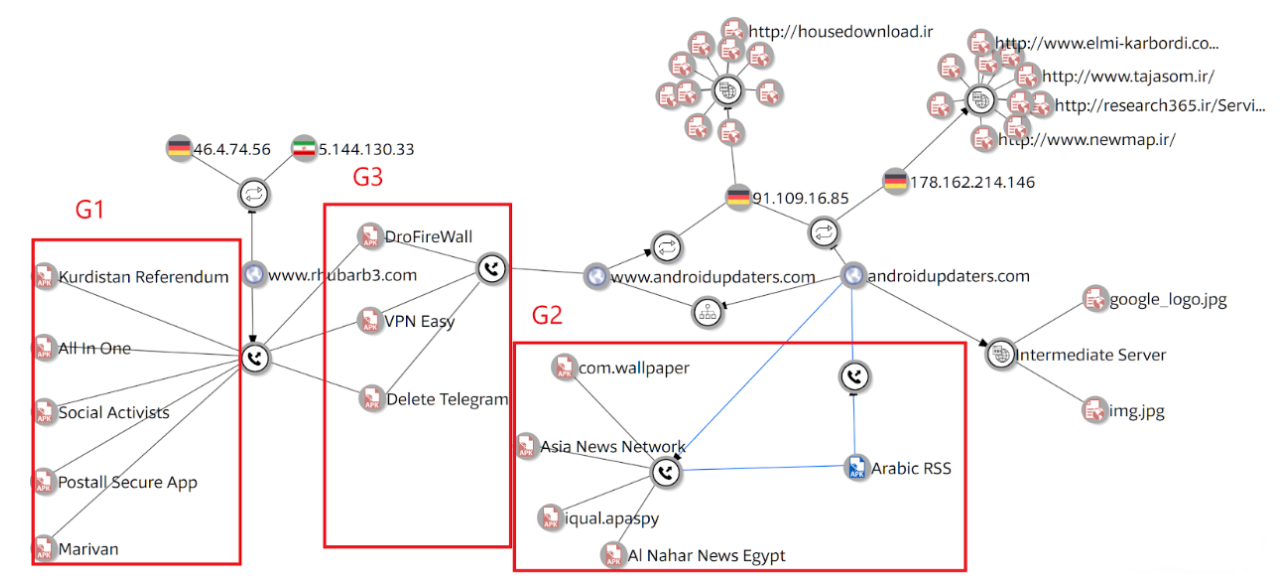
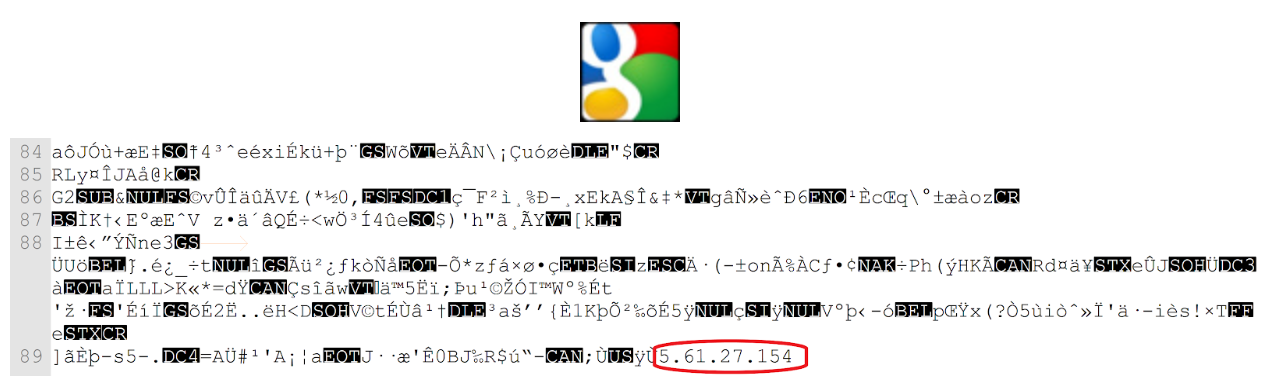
The ArabicRSS Trojan takes its C&C server address from the “androidupdaters.com/img.jpg” file.
The “androidupdaters.com” domain serves as “Intermediate Servers” – another network node between the Trojan clients and their corresponding C&C servers.
As seen in the graph, the domains contained the ‘img.jpg’ and the ‘google_logo.jpg’ image files.
The ‘imag.jpg’ and the ‘google_logo.jpg’ image files contain the following IP Addresses: 5.61.27.154 and 5.61.27.157, on which the C&Cs where hosted.
The “androidupdaters” domains have been hosted on the following IP Addresses: 178.162.214.146 and 91.109.16.85.
The androidupdaters.com intermediate servers were accessed by a different Trojan payload that was found in three different applications – the G3 group. It is the most advanced payload in the network.
G3 payload contain the base URL www.rhubarb3.com for their C&C servers.
The rhubarb-n domains are common to another Trojan payload type, the G1 Trojan group, on which the URL acts as a C&C server for five other different applications. The G1 group is the oldest group and the simplest among them.
The “rhubarb-3” domains have been hosted on the following IP addresses: 46.4.74.56 and 5.144.130.33.
The servers using IP Addresses: 178.162.214.146 and 91.109.16.85 are located in Düsseldorf, North Rhine-Westphalia, Germany, and are hosting several Iranian domains.
Among these domains, there are sites of Iranian Educational consulting system, student research groups, aerial imaging and an Iranian-Korean content download portal.
Technical Analysis
Let us review the Trojan types and the “Trojanized” applications. Readers who are not interested in the technical analysis are encouraged to skip to the “Summary and Conclusions” section.
G2 Group
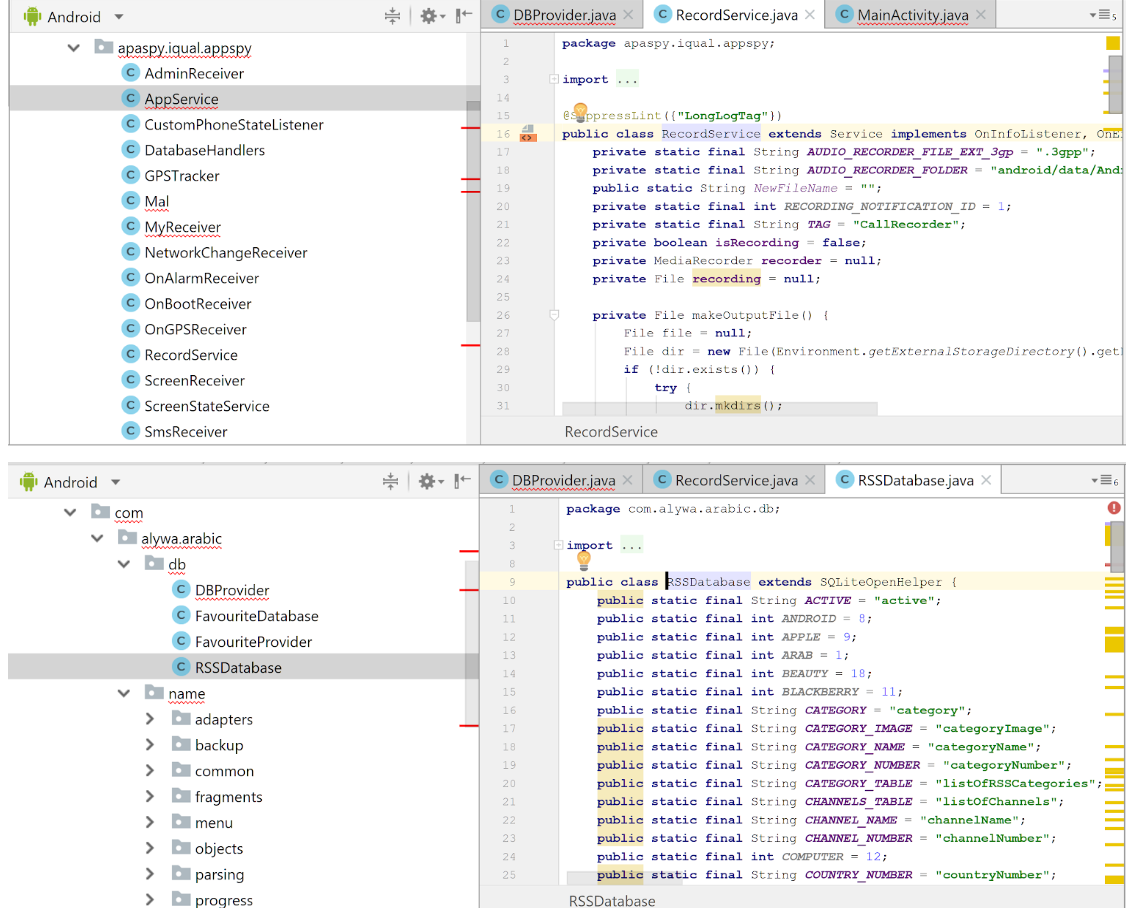
Spymaster Pro based spyware/backdoor. The code is under the package name of apaspy.iqual.appspy.
The Trojan provides various spyware functions of sending and monitoring: contacts, SMS messages, call logs, device location, device information, account details, images from the DCIM (Digital Camera IMages) directory. Additional spyware functions of location tracing, call recording, regular surround recording – triggered by the screen being off.
Trojanized applications:
- com.alywa.arabic.name – the Arabic RSS application
- alnaharegypt.news – the Egyptian ‘Al Nahar’ magazine application
- com.ann.newspaper – The Asia News Network
- com.wallpaper – yet another ‘adults wallpaper” app.
- iqual.apaspy – yet another porn-malware app.
G3 Group
A more advanced and powerful spyware/backdoor payload was also assessed. It has stronger capabilities than the first Trojan payload; in addition to basic capabilities of the first Trojan type. Those capabilities require a root permission and specifically target rooted devices.
The code is under the package name of com.testunit.
With root permissions, the attacker will gain the following malicious capabilities:
- Keylogger that captures all text inputs, including passwords and safe, confidential and self destructed messages.
- Exfiltrate and monitor 3rd party applications: whatsapp, Telegram, Facebook Messenger, Snapchat etc.
Trojanized applications:
- free.vpn.proxy.unblock.android.easy.app – VPN Easy – offers “free” VPN services.
- com.del.tele.acc – delete telegram account application.
- ltd.banehappy.drofirewall – DroFireWall is a front-end application for performing several system level operations. Most of those actions are not allowed to be executed without a root permission and/or the Device Admin Support: iptables Linux firewall management, Display blocked packets, control traffic within the local network or while being connected through a VPN, manage system applications and more.

G1 Group
Minimal spyware payload running within a single service.
The G1 Group is the parent of the G3 group. Goals of the malware include:
- Exfiltrate data of call logs, SMS, contacts, location, accounts, camera silent shot and device info.
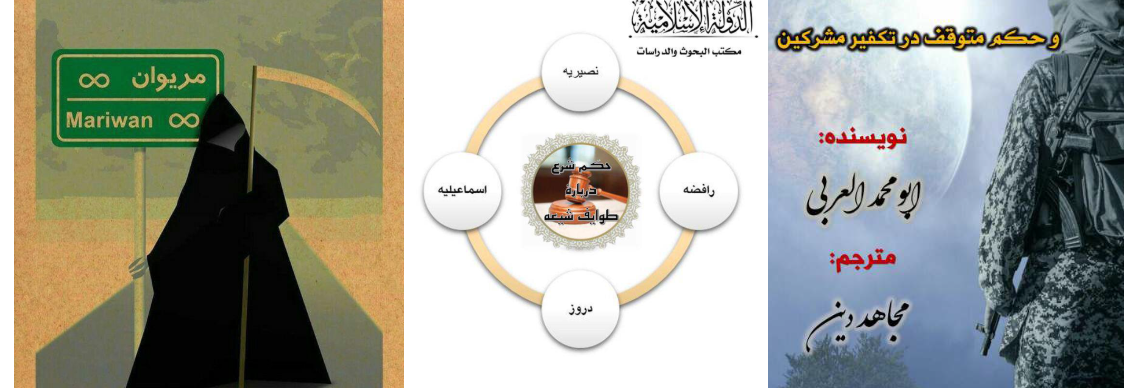
- The applications contain content about supporting the residents’ protest in the Kurdish-Iranian region, a communique against radical Islam and its use for control of the common people and more moderate issues about the Islamic religion and regimes in the Middle East.
Trojanized applications:
- com.majale.majale2 – Islamic Journals #2. A collection of articles about moderate Islamic issues, like:
-
- The banning the Takfir – a Muslim who accuses another Muslim of apostasy according to the Muslim religion.
- The verdict (Fatwa) of religion about Shi’a groups.
- Excuse of ignorance under the scrutiny of (Islamic) religion.
-
- com.app.kampynmariwansanandaj – Marivan, human rights activity in the Marivan-Sanandaj region at the Iranian-Kurdistan-Iraq borders.
- com.example.allinone – “all in one” messenger. The application mimics an application that is purported to manage all instant messaging in a single application. In reality, it takes the user name and password and sends it to the rhubarb3 C&C. The application contains evidence relating to some all-in-one application and an older version of the above Islamic Journals.
- com.app.postrall – Postal Secure App.
- com.app.referendumkurdistan – Application that is related to the independence referendum for Iraqi Kurdistan.

Trojan Vessel Application Types
It is worth noting there are several types of applications chosen to be vessels for the Trojan malware:
- Legitimate, free applications available on the official app store. This is the most innocent looking form of the Trojan because at first glance the app looks familiar (and therefore “safe”). The disadvantages of this approach, from the attacker’s perspective, are the Trojan is more “noticeable” due to:
- The original application being available on the Google Play Store. The Trojanized fake application would most likely forbidden from being published on the Google Play Store in the first place, due to copyright infringement. The user needs to be enticed into sideloading the app onto a device that enables running apps from unknown sources.
- The extended permission set. In the ArabicRSS instance, the Trojanized app is requesting 64 different permissions while the original asks only for three.
- The dangerous permission set, especially the BIND_DEVICE_ADMIN.
- The amount of receivers registered to almost all device actions under the intent-filters. In the ArabicRSS instance, the Trojanized app is being triggered by 29 actions while the original reacts for only four.
- “Adult” application is the most common vessel for a malicious payload, but it usually functions as adware or as ransomware. The infection rate is higher and the original application looks more like the Trojan and therefore, less “noticeable” due to:
- People don’t like to pay for software. The Trojanized fake app is free.
- The original and the malicious versions look similar in aspects of permissions and receivers. Free fake applications, without the Trojan payload, usually gain revenue by aggressive advertising, adware manipulations or trading with personal data. In order to keep running in the background and pushing ads, the app requires many permissions and subscribes on multiple receivers.
- Security tools. It is actually very common for several reasons:
- The information that one side wished to hide is what the side that the information has been hidden from wishes to reveal.
- Security tool applications might need root permissions in order to function properly.
- Root permission applications. In many cases, applications requiring root permissions are forbidden from being published on an official app store. As a result, those applications are often installed as sideload applications. Root permission can provide more spying capabilities like:
- Being more invisible to the user.
- Surviving deletion or even a factory reset.
- Disabling threats like anti-virus apps and system application management services.
- Bypassing system restrictions of recording, finding location and staying alive in the background without any icon or notification, key-logger, spy on 3rd party applications like WhatsApp, Telegram, Facebook Messenger etc.
Trojan Code Analysis
Let us examine the decompiled code of the ArabicRss.apk spyware. The application contains two fully functional code parts:
- The original ArabicRSS 3.4.1 application code all placed under the com.alywa.arabic package.
- The spyware code, based on the reverse engineering of an older commercial spyware Spymaster Pro placed under the apaspy.iqual.appspy package. The iqual is the common name in both spymaster and the Trojan packages.
Trojan at Work
Any complete spyware app needs to have specific base capabilities:
- Know where the C&C should be addressed.
- Have a communication protocol between C&C and the agent.
- Stay synchronized with the C&C for the data transfer. Be able to monitor the data, keep it “indexed” and send all of the data or parts of it again.
- Know how to handle the collected data, how much of it to store and when to send it.
- Keep being responsive, be ready to take orders in time.
- Staying undiscovered.
Let us review how the above are achieved. There are many data collection and active actions, so we will review just a small part that will indicate the whole lifecycle workflow.
“Keep Alive”
The application needs to run in the background, performing the task of spying without exposing any evidence of its existence.
While some spying tasks like monitoring SMS and call log can be triggered by registering a Broadcast Receiver to the Intent broadcasting, other tasks like location tracing and web browsing monitoring are tasks requiring some work without any wakeful event.
Other tasks consuming more resources such as CPU time and memory, for example, communication with the C&C servers, need to run in the background without any notifications.
The backbone of the Trojan work will be performed on the ‘AppService’ and ‘Mal’ main service classes, implementing a wakeful IntentService. Most of the resource-consuming tasks will be performed on top of these services. For simplification, we will refer both worker services as a single service.
Let us review the Trojan workflow:
- Most of the main device actions producing action Intents are caught by the ‘MyReceiver’ Broadcast Receiver class.
- The main AppService is launched if it isn’t already running.
- Some of these actions’ data, like calls and SMS traffic, are stored in real time in the local database. Most of the data is collected by single activity receivers. For example, a PhoneStateListener implementation monitors the call logs and manages the recording service as will be presented at the ‘Data Collection’ section below.
- The AppService executes several resource-consuming actions:
- Checks the current data collection status and check with the C&C if this data is up to date on the C&C side.
- Collects data that has no action Intent like location monitoring, web browsing and contact storage modifications.
- If an Internet connection is available on the device, the service sends any collected data not sent previously.
- Any data that was not sent and accepted at the C&C will be sent.
- In a case of an idle device, the Trojan will wake the device repetitively by the AlarmManager the AppService will be launched on device reboot.
Code: apaspy.iqual.appspy.MyReceiver, AppService, OnBootReceiver components at AndroidManifast.xml at Trojanized ArabicRSS.apk – package com.alywa.arabic.name, version 3.4.1
Code: apaspy.iqual.appspy.MyReceiver, AppService, OnBootReceiver java code at Trojanized ArabicRSS.apk – package com.alywa.arabic.name, version 3.4.1
Who’s the Boss?
A Trojan payload, like any typical spying agent, needs to receive orders and needs an endpoint to deliver the collected information.
As we previously discussed, the C&C server is the server that manages the Trojans. The Trojan in our case study is a payload in a legitimate Android app, but the C&C can typically manage payloads of other platforms like iPhone, PC, Mac, Smart TV, etc.
The C&C address might change in order to avoid detection activity or due to technical maintenance reasons.
One of the techniques of setting the C&C address is by the intermediate server.
The ‘androidupdaters.com/img.jpg’ image file contained inside 5.61.27.157, the IP address of the C&C server.
Code: findServer function at apaspy.iqual.appspy.Mal at the Trojanized ArabicRSS.apk – package com.alywa.arabic.name, version 3.4.1
Once receiving the C&C address, the specific spying configuration is pulled from the server using the IMEI as the identifier.
String urlString = Mal.Server_Domain + “/spyMobile/upload.php?imei=” + imei;
Data Collection Management
Let us observe the call log monitor and call recording, as an example.
A PhoneStateListener implementation saves call log records to the local DB and manages the background recording service.
The main (simplified) collection behavior:
- A “phone state changed” event is received.
- If the phone is ringing or ‘CALL_STATE_OFFHOOK’ the ‘Record Service’, an Android Service that will utilize the MediaRecorder, is started.
- The recording size is limited to 30% of the total available space.
- If the phone state is idle then:
- The call duration, number, direction and date are saved to the local DB.
- The call recording will be stopped if it was not stopped by other means, like failure or exceeding the size limitation.
- The call recording file is split into smaller pieces.
- The call log and the audio recording files are sent to the server if an internet connection is available.
- If the data was successfully sent and accepted at the C&C the data is deleted from the local storage.
- If an internet connection is not available at the time of saving, another sending procedure of the collected data will be committed by the AppService (as described at the ‘Staying Alive’ section).
When the AppService queries the C&C for the status of the call log commands, it might get a command to send all the call logs that are on the device. The ‘send all’ command is typically sent when the Trojan is first executed. However, in the western world’s legal system, there might be a legal permission for monitoring a targeted person’s data and not to get all the past data. Since the Trojan is based on commercial spyware, it might be that the optional ‘send all’ is inherited from there.
Although it is wise to send big recording only while being connected to WiFi, we didn’t witness this behavior.
A plain surrounding recording (not phone calls) is performed for several seconds after the device screen is turned off.
Trojanized ArabicRSS.apk. package com.alywa.arabic.name, version 3.4.1, apaspy.iqual.appspy.CustomPhoneStateListener code
Trojanized ArabicRSS.apk. package com.alywa.arabic.name, version 3.4.1, apaspy.iqual.appspy.RecordService and ScreenReceiver code
Summary and Conclusions
The Watering Holes attack vector can be very effective. It covers a big group containing targeted people due to:
- The targets are coming to you, there is no need to reach them.
- It gains enough data that can be used for link analysis and other data analysis methods that might lead to additional targeted surveillance. Although the infection rate might not be high, when attacking a large amount of people, the total infected devices might provide enough intelligence.
- It is cheap to buy, develop and maintain compared to the usage of zero day exploits and first class offensive cybersecurity companies.
Once the application is on the device, we have shown how the espionage actions are easy to perform.
I would be remiss if I didn’t mention, we are protecting our clients from these attacks and attacks like it. Our Zimperium platform leverages our award-winning, disruptive and patented machine learning-based engine, z9, to protect mobile data, apps and sessions against device compromises, network attacks, phishing attempts and malicious apps.
Our z3A Advanced App Analysis reports continually evaluate mobile app risks, providing insight into the our client’s employees’ apps. Clients can see which apps in use are safe or risky, and set security policies to reduce that risk. For each risky mobile app identified, we provide deep intelligence, including contextual analysis, as well as privacy and security ratings.
Acknowledgments
We would like to thank Asaf Peleg for the management of this research. Some of the data that was gathered by utilizing Virustotal and Wayback Machine. We hope that you enjoyed your reading. Be aware of threats of unsafe device usage, especially while being thirsty around the Watering Holes 😉.