What is DoubleLocker?
Security researchers at ESET discovered a new ransomware infecting Android phones called DoubleLocker. DoubleLocker is an exploit that encrypts data on the infected device and then changes the device PIN to a random number. Victims remain locked out of their device unless they pay a ransom to the hackers.
DoubleLocker spreads in the very same way as its banking parent does. It is distributed mostly as a fake Adobe Flash Player through compromised websites.
Once launched, the app requests activation of the malware’s accessibility service, named “Google Play Service”. After the malware obtains the accessibility permissions, it uses them to activate device administrator rights and set itself as the default Home application, in both cases without the user’s consent. [1][2]
How zIPS Helps
Zimperium’s z9 on-device mobile threat defense engine is trained in a lab using machine learning techniques. These techniques are applied at the device, network, and application threat vectors to specifically look at operating system level statistics. These statistics determine if a threat is occurring on the device and has enabled us to detect 100% of both known and previously unknown attacks. Should an attempt to exploit the device be detected, Zimperium can take action on the device to prevent the exploit from advancing.
zIPS is a mobile security app containing the z9 detection technology. zIPS monitors the entire mobile device for malicious behavior regardless of the attack entry point. The device-wide resident approach does not rely on external IDs or malware signatures. This makes zIPS immune to evasion techniques such as polymorphic malware, virtual machine awareness, download and execute techniques or binary obfuscation.
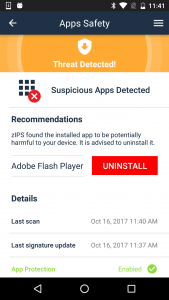
zLabs tested the recently discovered DoubleLocker malware disguised as an Adobe Flash Player update. We found zIPS detected the malware and provided user recommendations to uninstall the specific app. The screen shots below show the malicious Adobe Flash Player app asking for Bitcoin followed by zIPS detection and recommendations.
Additional Recommended Actions
We recommend utilizing a mobile threat defense app like zIPS to detect operating system vulnerabilities, file system changes, mobile malware and device modifications as well as network threats. You can install zIPS from Google Play or Apple App Store. After installation, please contact Zimperium for an evaluation license and administration console.
Zimperium also advises you to update your devices with the most up to date operating system and security patches available. You can read the latest security updates from Apple and Google on their respective security sites.
Contact Us
If you have additional questions on this threat or others that may be affecting your users, please contact us so we may answer your specific questions.
- Inquiries: zimperium.com/contact-us
- Customer Support: support.zimperium.com
Sources:
- https://www.welivesecurity.com/2017/10/13/doublelocker-innovative-android-malware/
- https://news.drweb.com/show/?i=11381