Speaker: JT Keating, Zimperium’s Vice President of Product Strategy
Real World Examples: Protecting an Oil & Gas Company from Mobile Threats
Speaker: JT Keating, Zimperium’s Vice President of Product Strategy
Real World Examples: Mobile Threats Detected at a Hospital
Speaker: JT Keating, Zimperium’s Vice President of Product Strategy
Can a Corporate Network Get Hacked Via a Smartphone? Hint: Yes! Here’s How It Happened
Speakers: Andrea Pierini (Penetration Tester) and JT Keating (Zimperium’s Vice President of Product Strategy)
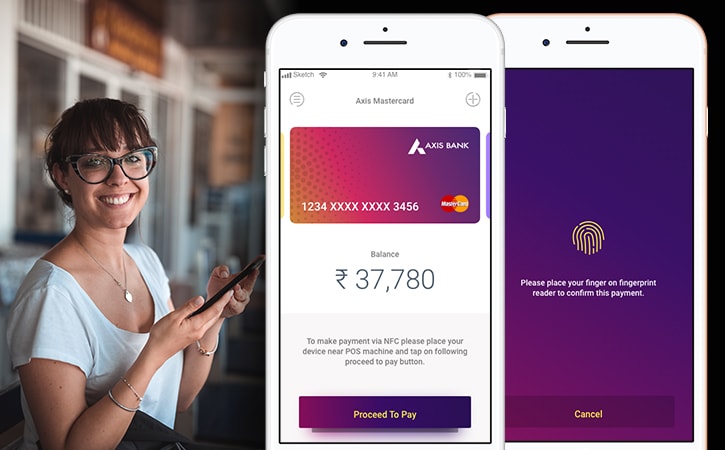
Real World Examples: Defending Against Mobile Threats at Two International Financial Services Firms
Speaker: JT Keating, Zimperium’s Vice President of Product Strategy
Real World Examples: Protecting City Government Employees from Mobile Threats
Speaker: JT Keating, Zimperium’s Vice President of Product Strategy
Real World Examples: Protecting Client Data from Mobile Threats at an International Consulting Firm
Speaker: JT Keating, Zimperium’s Vice President of Product Strategy
Real World Examples: Mobile Threats Detected at Law Firms
Speaker: JT Keating, Zimperium’s Vice President of Product Strategy
The Mobile Menace Most Wanted List: #1 OS Exploits
Speaker: JT Keating, Zimperium’s Vice President of Product Strategy
The Mobile Menace Most Wanted List: #2 Rogue Profile
Speaker: JT Keating, Zimperium’s Vice President of Product Strategy
Categories
- Analyst Reports 11
- Case Studies 12
- Data Sheets 2
- Infographics 20
- News 316
- Press Releases 87
- Resources 47
- Solution Briefs 29
- Videos 16
- Webinars 153
- Whitepapers 63