We’ve all seen them. They are annoying; can be abusive and sometimes malicious.
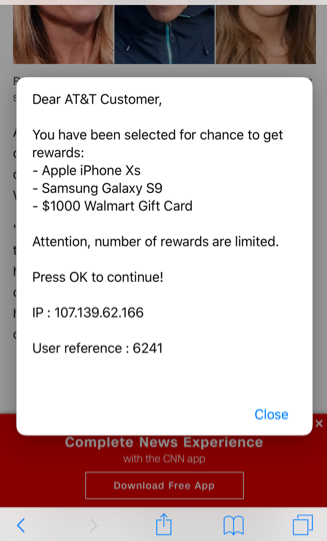
It goes something like this: You’re navigating a web page to read an article on your mobile phone. Just as you start to read, the whole page is redirected. A full screen ad announces you’ve just won $1,000! Lucky you!
Not really.
These types of ads are known as full page redirect advertising. They are nothing more than a scam. The culprits are companies pushing offending Javascript code in their ads. With millions of advertisements being created and pushed to ad networks every day, ad networks are generally overwhelmed. They do a poor job at screening this offending content, which is often obscured or cleverly hidden. Vetting is a challenge and these scam ads slip through.
It’s a minor annoyance at first. However, there are times when you realize you’re being redirected. So many times you can’t get back to the original article. Now it’s more than just an annoyance!
You have to close the browser window and open a new page to get back to the original article. Even if you do get back to the article, chances are you’ll get the same pop up again.
How could this happen in the modern age?
These types of ads have become more prevalent on mobile devices because there generally aren’t any ad blockers installed. Safari and Chrome both can suffer from the same issue. While there are mobile ad blockers available, most users don’t know how to turn them on. Some publishers even require disabling ad blockers to view the content on the page, because blocking impinges on revenue streams.
The larger publishers and websites aren’t immune to these ads, relying on the ad networks to fund their businesses. If the ad networks don’t catch it, then CNN – or any other site – can unknowingly redirect their users to the latest abusive full-page pop up. Unfortunately, this creates a negative user experience that hurts business. Publishers cannot review every ad in real time, meaning the advertising networks must take on the responsibility.
More than just annoying and abusive – it’s malicious
Full page ads also may have a more malicious intent. Some ads have malware included. You may think you’re clicking to exit the pop up, but the exit button is a disguised malware payload you end up downloading. Adding it all up, even large publishers now could unintentionally be sending you to a malicious payload!
This presents a particularly bad problem for enterprises where users are bringing their own devices (BYOD). Malicious ads can inadvertently trigger corporate compromises. User devices connecting to corporate networks could be infected, which then potentially puts corporate data or network connections on the device at risk.
How can you stop it?
You should definitely consider installing an ad blocker on your mobile device. You probably already have one on your desktop. There are many good ones available in the app stores for iOS and Android.
You could also use a different browser than the default ones shipped with your phone. Purify and Firefox have mobile browsers with additional privacy and ad blocking features enabled by default.
Ad blockers only solve part of the problem. If you end up disabling an ad blocker to view content, you still could expose yourself to malicious content. Mobile devices need protection too, just like your desktop.
It is clear mobile devices cannot be an unprotected endpoint for organizations because it has all of the access and contains all of the information of a traditional endpoint. And while there are some overlaps in what you protect – email, calendars, etc., – the way you solve the traditional endpoint security problem is completely different than how you solve the mobile security problem.
The Zimperium platform leverages award-winning, disruptive and patented machine learning-based engine – z9 – to protect mobile data, apps and sessions against device compromises, network attacks, phishing attempts and malicious apps.
To date, z9 has detected 100 percent of zero-day device exploits in the wild without requiring an update or suffering from the delays and limitations of cloud-based detection or legacy security architectures—something no other mobile security provider can claim.
Josh Scott is Vice President of Product Management at Zimperium. His background in cyber security extends from incident response, vulnerability management, pentesting, and everything in between. Josh has designed and helped build multiple software platforms focused on serving enterprise cyber security needs, where environmental adaptation and flexibility are essential.