By: Zuk Avraham and Rachel Ackerly
Is Google abandoning their customers?

A recent policy change at Google to stop producing security updates for Android 4.3 or older could jeopardize roughly 930 million Android users. This translates into about 60% of all Android users, many who would never realize they were even exposed or vulnerable in the first place. What does this mean for enterprises around the globe that deploy broad BYOD programs predicated on employees choosing and paying for their own mobile devices?
This great news for hackers, bad news for consumers, and possibly worse news for enterprises, was not announced by Google but rather discovered and shared by security researchers Tod Beardsley and Joe Vennix from firm Rapid7. When the security researchers notified Google about the unpatched Android vulnerabilities they were surprised to learn of the policy change.
Per Google, “If the affected version [of WebView] is before 4.4, we generally do not develop the patches ourselves, but welcome patches with the report for consideration…” “…Other than notifying OEMs, we will not be able to take action on any report that is affecting versions before 4.4 that are not accompanied with a patch.”
Google has decided to only fix bugs found in the two most recent versions of Android known as Kitkat (4.4) and Lollipop (5.0).
What is the Vulnerability?
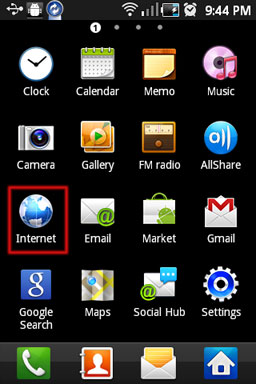
Researchers at Rapid7 have successfully bypassed WebView’s Same Origin Policy in Android Jelly Bean, versions 4.0-4.3, and earlier. WebView is the component used to render websites on Android devices. This could just be the tip of the iceberg for unsuspecting Android users. The implications for users who bring these unprotected devices into their offices and corporate networks is alarming.
What is the Impact?
Employees utilize mobile devices to access organizational systems and critical business applications both on and off the corporate network. These systems contain sensitive data that if exposed could result in data security breaches and revenue loss for an organization. An Android device running 4.3 or older can easily be manipulated to bypass Same Origin Policy and allows the hackers to access confidential data of websites and services that the user is already logged into.
According to Zimperium Founder, Chairman & CTO, Zuk Avraham, “Same Origin Policy bypass vulnerabilities can be triggered during a Man-In-The-Middle or phishing attack. The attack runs in a hidden iframe and can utilize any unencrypted traffic to read the content of encrypted traffic, after being decrypted on the victim’s browser. This process essentially makes SSL useless in services that the unsuspecting users are logged into.”
SOP protects websites that are not in the same protocol, port and domain to read the content of other websites. By successfully bypassing SOP, an attacker can run HTML code in a user’s browser (via MITM/phishing) – and read the content of any website a users is logged in to – even if the website is running a different protocol (https vs. http), port (443 vs. 80) or domain.
This policy change by Google puts the onus on OEMs to identify and deliver security updates to protect their users. It’s then up to the OEMs to patch their respective devices and ensure the OTA updates are delivered by carriers. The question is what level of follow-through and security should users running older versions of Android expect? Whose responsibility is it to notify the end-user who likely never thinks about the security of their phone unless it stops working correctly.
Verizon, AT&T, Sprint-Nextel and T-Mobile have also been called out for their reluctance in patching Android vulnerabilities. The complaint asked the FTC to force carriers to warn users about unpatched vulnerabilities and give customers the option to leave their carrier contracts behind in such cases, without penalties.
With more and more personal devices being used in the workplace it is only a matter of time before this simple support decision by Google will impact Enterprises around the globe. The reality is the majority of those 930 million users likely don’t even know they are exposed and every MITM attack or link they open exposes them to the SOP bypass vulnerability – begging the question – who is paying attention? To mitigate against enterprise security risks, IT Security Administrators need to balance employee enablement with IT control that provides continuous protection for mobile devices against known and unknown threats. Zimperium Mobile Threat Defense customers are immune to this threat in public network regardless of the Android version of the device.
Zimperium offers enterprise class protection for mobile devices against the next generation of advanced mobile attacks. Zimperium is the first and only company to provide a complete mobile security system that continuously runs on the device to provide visibility, security and management for iOS and Android devices. With its non-intrusive approach, users can be confident that their data and their privacy are protected at all times—both on and off the corporate network.

