Secure coding for mobile apps refers to writing code with security in mind, using technical measures and best practices that prioritize protecting user data from unauthorized access, disclosure, or modification. Secure coding is integral to maintaining users’ trust while safeguarding data.
Secure Coding Best Practices
- Encryption: To protect sensitive data on-device and transmitted over networks (TLS/SSL), developers should use robust encryption algorithms like AES and securely store encryption keys so attackers cannot easily compromise them.
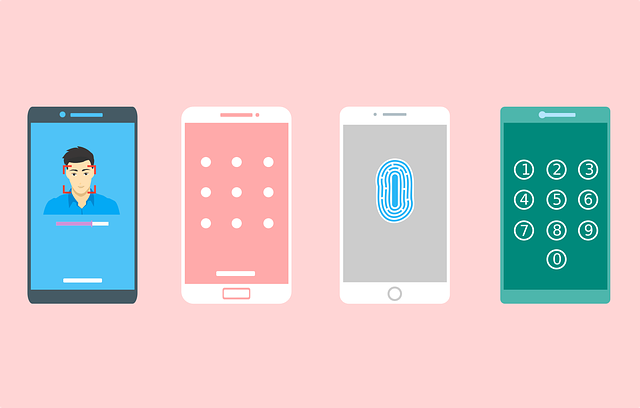
- Authentication and Authorization: Implement strong authentication and authorization processes so your information stays safe. Implement user authentication mechanisms (e.g., multi-factor authentication) to validate the identity of users, as well as enforce proper authorization controls to ensure only authorized individuals can access data and features.
- Input Validation: Validate and sanitize user inputs to safeguard against common security vulnerabilities like SQL injection, Cross-Site Scripting, Cross-Site Request Forgery (CSRF), and data injection attacks. Unsanitized inputs should never execute code.
- Secure Communication: Use secure protocols (HTTPS) for all data transmission between the mobile app and backend services. Validate server certificates to prevent man-in-the-middle attacks.
- Secure Storage: On iOS and Android platforms, use platform-specific secure storage mechanisms (e.g., Keychain or Keystore) to store sensitive information (passwords, API keys, or tokens) safely. Avoid storing this sensitive data in plain text or easily reversible formats like JSON.
- Code Review and Testing: Conduct regular code reviews to detect security vulnerabilities and correct coding errors, use automated security scanning tools (e.g., static analysis tools or dynamic analysis tools) to identify potential security holes, as well as session management for optimal session control.
- Secure Session Management: Create and validate strong session tokens. Validate them after logout or an extended period of inactivity to prevent session tokens from expiring prematurely and becoming invalidated.
- Error Handling: When dealing with errors and logs, do not reveal sensitive data that could compromise security. Implement proper error handling to safeguard information leakage and strengthen resilience against attacks on mobile apps.
- Secure APIs: Protect mobile app APIs using authentication and authorization mechanisms that comply with industry best practices; validate responses gracefully for errors to avoid security concerns.
- Code Obfuscation: Use code obfuscation techniques to make it more difficult for hackers to reverse engineer your mobile app and discover vulnerabilities.
- Patch Management: Stay up-to-date on security patches for third-party libraries and frameworks with known vulnerabilities in your app.
- Security Headers: Implement security headers, such as Content Security Policy (CSP) and HTTP Strict Transport Security (HSTS), to protect web views and browser components within an app.
- Secure Third-Party Integrations: Reviewing third-party libraries and SDKs used in an app’s security architecture and ensuring they comply with secure coding standards is vital for user education and incident response planning. Involve the users in developing strong password management policies and keeping mobile devices updated to prevent issues in future updates.
- Incident Response Plan: Develop an incident response plan to address security and data breaches quickly and efficiently.
Additional Steps to Ensure Your Mobile App is Secure
Here are additional steps you can take to make sure your mobile app is secure:
- Start with a Secure Development Framework: Begin with a secure coding framework or set of guidelines, such as the OWASP Mobile Application Security Testing (MASVS) or the OWASP Mobile Security Project. These resources provide best practices and checklists for mobile app security.
- Threat Modeling: Conduct a threat modeling exercise to identify potential security threats and vulnerabilities specific to your app. Threat modeling helps you understand your app’s attack surface and prioritize security efforts.
- Secure the Backend: Ensure your backend services, APIs, and databases are secure. Implement proper authentication, authorization, and data validation on the server side to prevent unauthorized access and data manipulation.
- Data Encryption: Developers should encrypt sensitive data at rest and in transit. Use industry-standard encryption algorithms (e.g., AES for data at rest, TLS/SSL for data in transit).
- Secure Code Development: Follow secure coding practices, including input validation, proper error handling, and secure storage of sensitive data.
- Secure Offline Usage: Consider how your app behaves when offline. Ensure that sensitive data remains protected even when the device is not connected to the internet.
- User Education: Educate users about best security practices, such as creating strong passwords, logging out of the app when not in use, and being cautious about sharing personal information.
- Regular Updates: Keep your app and all its components (libraries, frameworks, SDKs) up-to-date. Security vulnerabilities are discovered and patched regularly, so it’s crucial to stay current.
- Regulatory Compliance: Ensure your app complies with relevant data protection and privacy regulations (e.g., GDPR, HIPAA) if it handles sensitive user data.
- Continuous Monitoring: Implement continuous monitoring and logging to detect and respond to security incidents in real-time.
- Security Documentation: Maintain documentation that outlines your app’s security features and practices. This documentation can be valuable for audits and compliance checks.
Secure coding is an ongoing process, and developers should regularly assess and update their apps to address emerging security threats and vulnerabilities. By adhering to technical secure coding best practices, mobile app developers can significantly enhance the security of their applications while protecting user data against potential risks.
