“Security and risk management leaders who need to strengthen their mobile security posture should adopt MTD products to improve their overall security hygiene.” – Gartner
Gartner recently published the 2021 Market Guide for Mobile Threat Defense report, and the analyst firm continued to highlight the importance of enterprise adoption of Mobile Threat Defense (MTD) solutions for the evolving workforce. Zimperium is once again recognized by Gartner as a Representative Vendor, providing an advanced MTD solution to organizations of all sizes and bringing security confidence to mobile endpoints.
You can read Gartner’s 2021 Marketing Guide for Mobile Threat Defense here.
The past year has proven that as mobile endpoints continue to be part of the larger, evolving attack surface, the number of threats against them continues to rise as well. And as mobile continues to be adopted into everyday workflows, the avenues of attack will continue to be shown. The mobile endpoint’s security posture connected to corporate networks, both managed and unmanaged, needs to be addressed early on to avoid any of these devices becoming the starting point for a much larger security incident.
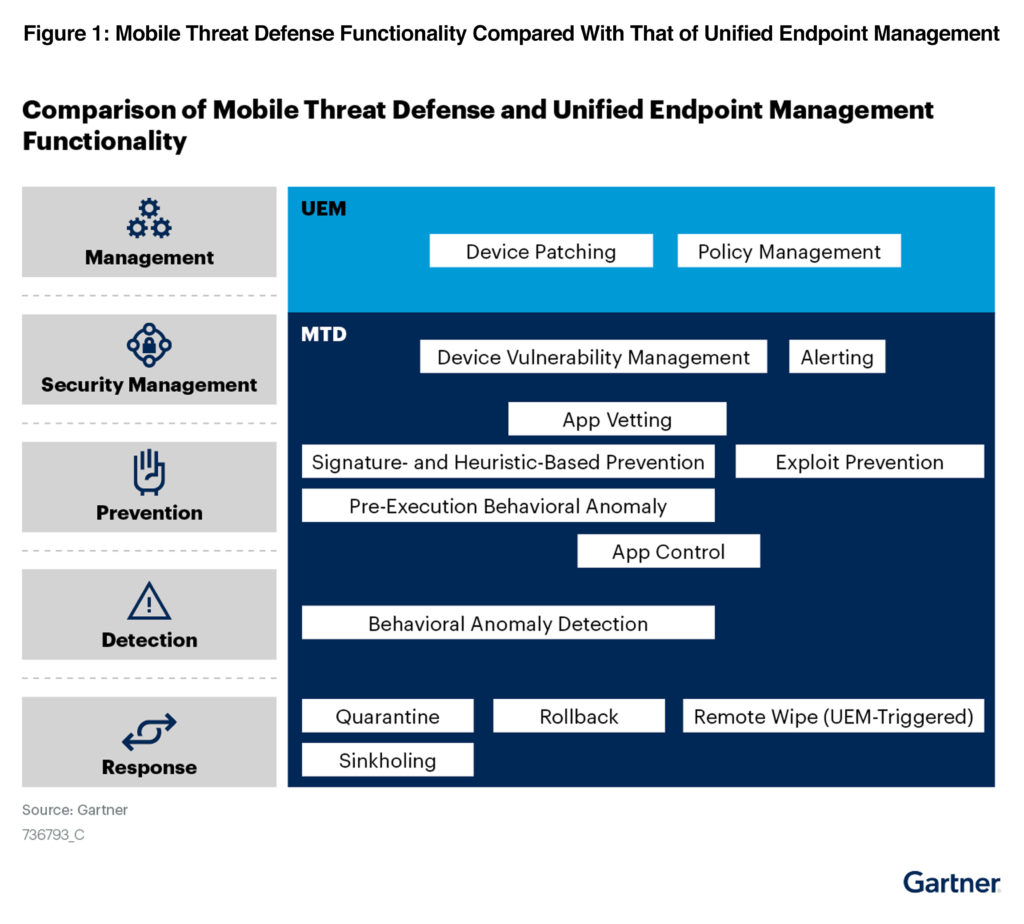
“MTD products not only prevent attacks but also detect and remediate them. MTD focuses on identifying and thwarting malicious threats, rather than relying on device management configuration to protect against simple user mistakes.” – Gartner
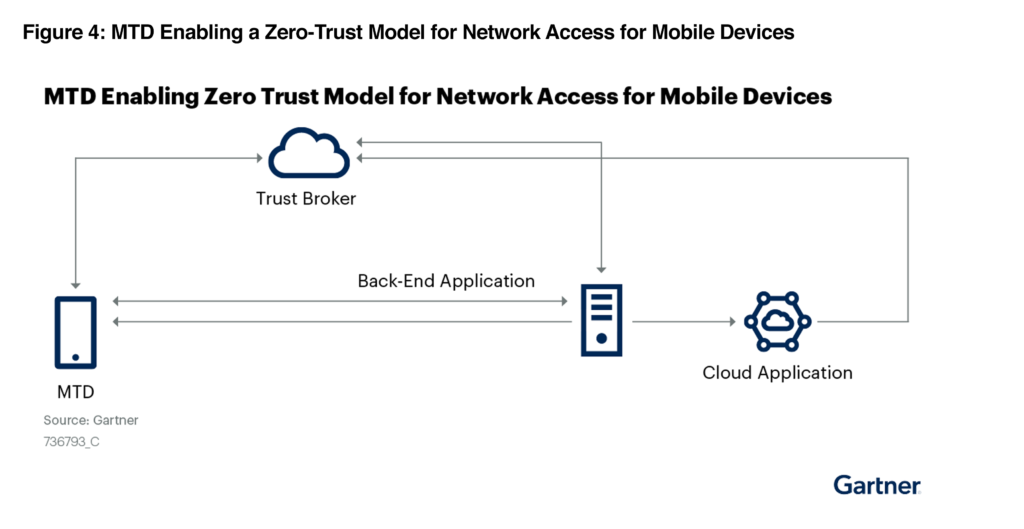
Mobile Devices Supporting Zero Trust
The last year also saw enterprises adopting more advanced security architectures, with many focusing on zero trust architectures. But as they address security gaps with various security technologies, they must also normalize mobile device security. Properly configured and integrated, advanced MTD solutions can enhance existing zero trust controls by providing mobile device risk attestation.
“Emerging use cases envisage MTD as a component of zero-trust network access (ZTNA) architecture and of an extended detection and response (XDR) system for detection and response, which can serve as a pilot for unified endpoint security. This is in addition to the use of MTD for mobile phishing protection.” – Gartner
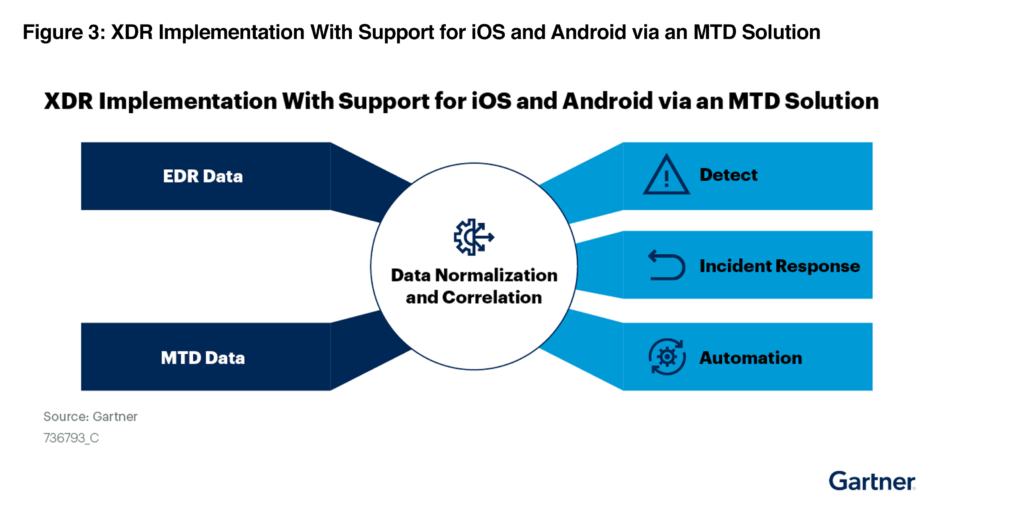
Mobile Forensics in XDR
According to the Market Guide for Mobile Threat Defense, enterprises need to adopt mobile defense solutions into their security stack supporting their zero trust architectures and extended detection and response (XDR) technologies. And as organizations continue to evolve with both remote and distributed workforce policies, so must their cyber hygiene and security mindset.
This integration and extended security capabilities are vital to shoring defenses for enterprises evolving from EPP to XDR security solutions. Advanced MTD solutions provide the features, workflow, and capability that complement XDR capabilities on mobile devices.
UEM & SIEM Integrations
Gartner also highlights the importance of UEM and SIEM integrations with the rise in MTD deployments, integrating as seamlessly as possible into existing security workflows. While EPP vendors are deploying lightweight mobile security applications, they often do not have the capabilities, strengths, and maturities to match existing MTD solutions’ effectiveness. Integration into existing systems, from UEM to EPP dashboards, is key to providing effective mobile security outcomes for security and IT teams.
“[Enterprises should] integrate MTD with incumbent unified endpoint management (UEM) tools. They should favor the app-based option and leave proxy-based deployment for corporate-owned business-only (COBO) scenarios.” – Gartner
“Usage of an MTD solution on top should aim not only to address advanced malicious threats but also to improve enterprise security hygiene.” – Gartner
Case for Purpose-Built Applications
IT and security leaders responsible for their enterprise’s mobile endpoint security should be aware that purpose-built mobile security applications are designed to do more than prevent attacks and bring a whole host of other advanced security features to the mobile devices. Zimperium zIPS, for example, is a hybrid machine learning endpoint application, providing both online and offline protection against phishing attempts, misconfigurations, malicious applications, and more across iOS, Android, and Chromebook devices.
“At the device level, the ability to assess postures, such as OS version, security updates, system parameters, device configuration, firmware and system libraries, to identify security misconfigurations, device vulnerabilities, and suspicious or malicious activity. For example, MTD tools can check for modification of system libraries and configurations, as well as for privilege escalation, such as a jailbreak or rooting.” – Gartner
And while legacy mobile security tools do exist, they lack the advanced approach to mobile endpoint security necessary to keep up with modern-day threats.
“[We] see no value in adopting antivirus solutions that do not provide behavioral anomaly prevention and detection, as the underlying mobile platforms already perform signature-based scans to look for malware.” – Gartner
As enterprises of all sizes evolve their security posture and workforce in unison, the priority to adopt advanced mobile threat defense toolsets like Zimperium continues to rise among security and IT leaders. The only way enterprises can shore up their zero trust to XDR architecture and gather the data they need to make informed decisions with their UEM and SIEM, is with advanced mobile endpoint device security.
What Now?
If you want to learn more about how Zimperium can help secure your devices and apps in all the frequent use cases and more, please contact us for a free mobile risk assessment and security consultation.
1 Gartner, Market Guide for Mobile Threat Defense, 29 March 2021. Dionisio Zumerle, Rob Smith.
Document ID: G00736793
Gartner Disclaimer
This graphic was published by Gartner, Inc. as part of a larger research document and should be evaluated in the context of the entire document. The Gartner document is available upon request from https://get.zimperium.com/gartner-market-guide-for-mtd-2021/