Every Industry's Battle: The Threat of Mobile Malware on the Enterprise
As we observed in our 2023 Mobile Banking Heists report, mobile banking apps have traditionally been a target for mobile malware due to the direct financial incentives for cybercriminals. But in today’s digital age, mobile applications have become the cornerstone of productivity, business growth, and user engagement in almost every industry beyond banking. Our research also shows that the 29 malware families we highlighted in the Heist report also target 478 non-banking mobile applications across 32 categories.
Let’s look at some stats that summarize our findings.

Top 10 targeted categories by number of apps
The following table shows the top 10 targeted categories based on the number of unique apps that are at risk. The number of downloads represents the potential victim base for malware authors.
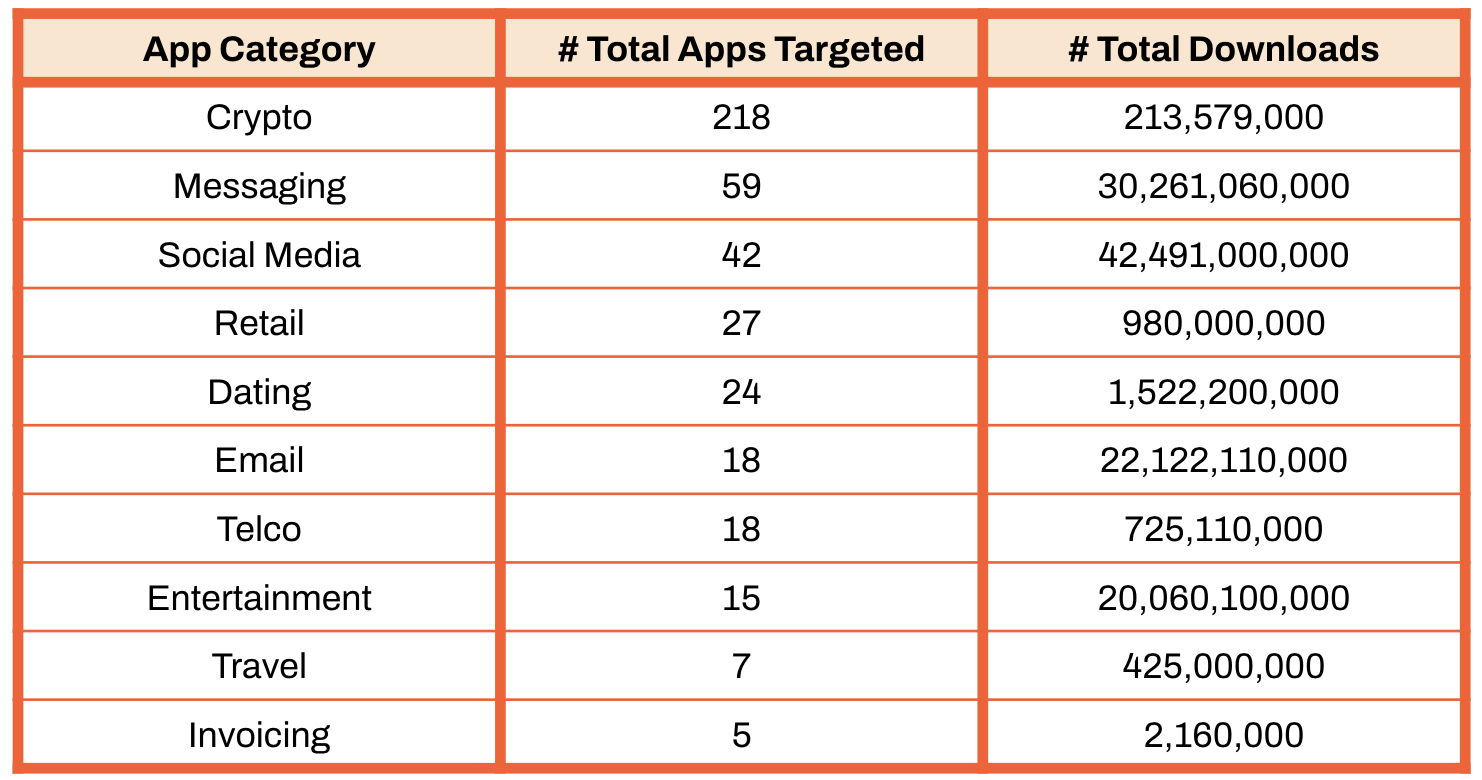
Interesting Fact: Malware intuitively targets the top three categories because they are high-value targets. However, ‘Invoicing,’ though lower in volume, is equally attractive. These apps often serve as entry points into larger business networks, allowing attackers to conduct more extensive data breaches or ransomware attacks. The high transaction volume and inherent trust in invoicing apps make them lucrative and susceptible targets, especially for small and medium-sized businesses that may need more robust security measures.
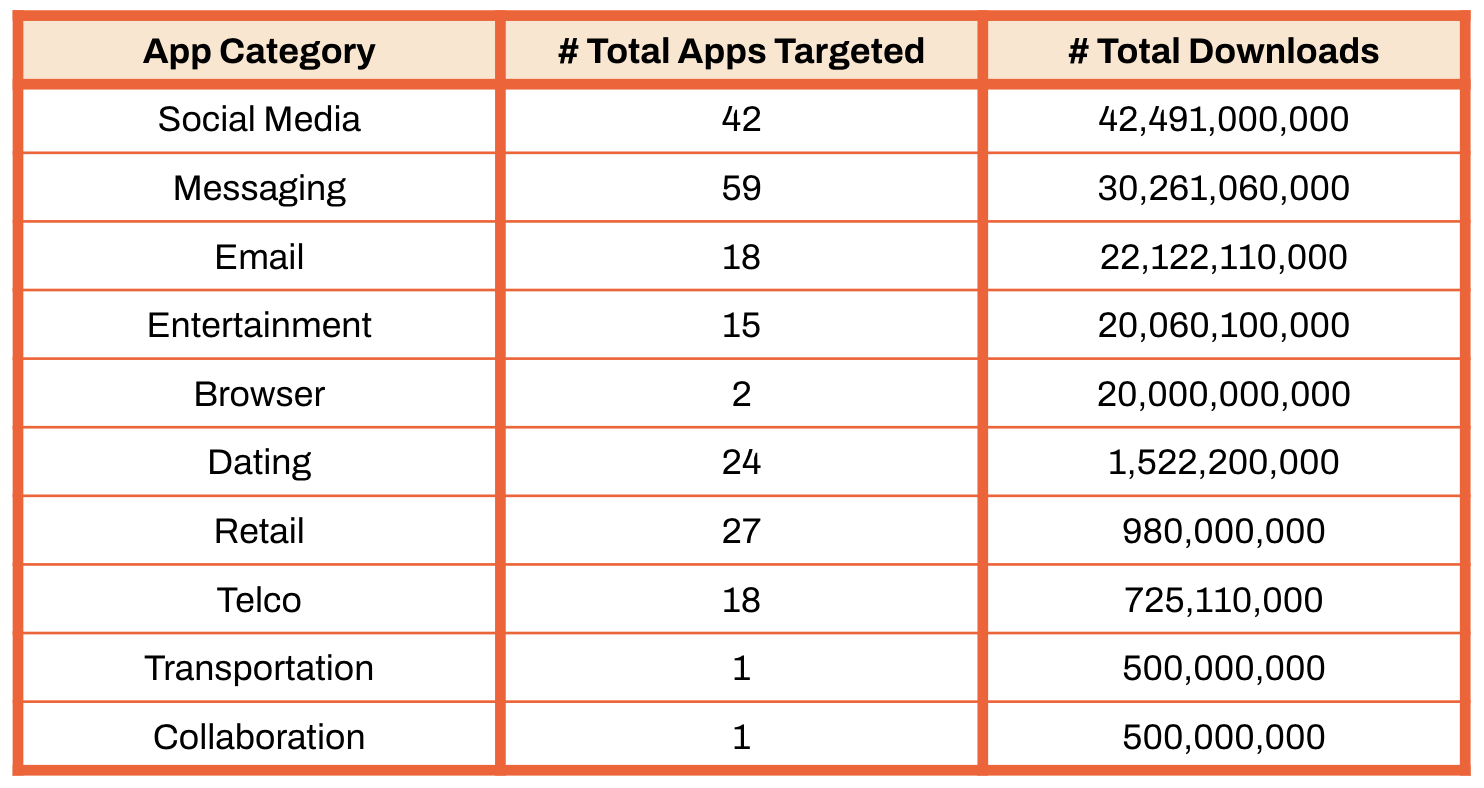
Top 10 app categories by total downloads
The following table shows the top 10 targeted categories based on the number of times the targeted apps in these categories were downloaded. The number of downloads represents the attack surface size for malware authors.
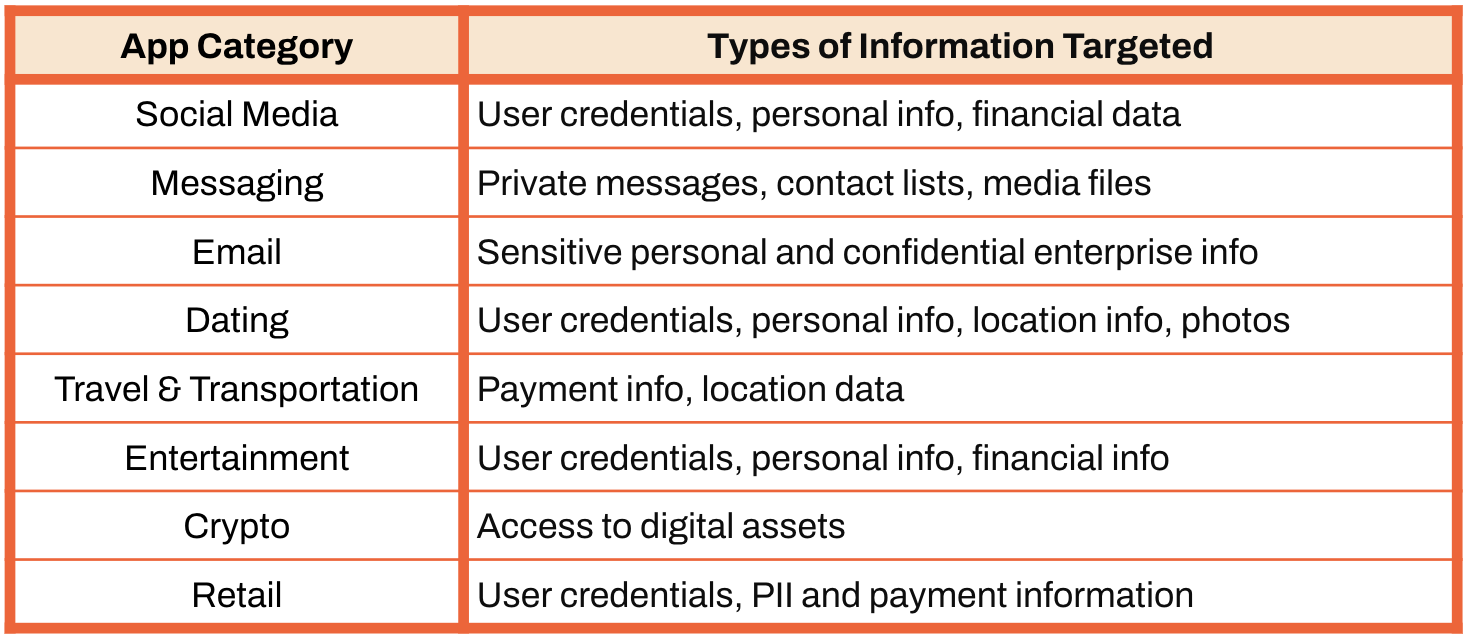
What makes these categories attractive to malware authors
Like traditional banking, these apps have massive global reach, PII info, payment info, access to digital assets, and enterprise secrets. Their appeal is amplified by network effects and cross-platform availability, making them integral to daily life for billions of users. Below are some examples of the type of valuable information attackers are after.
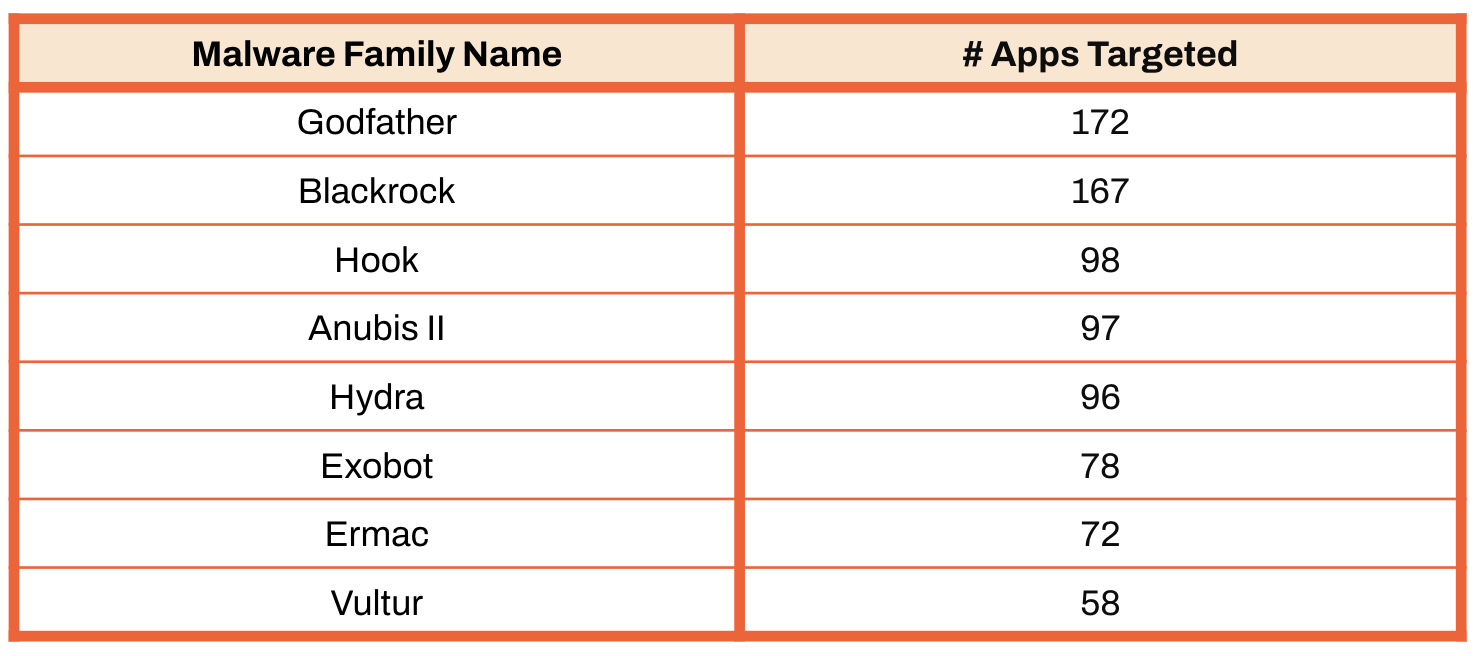
Malware families targeting most apps
Below are the top malware families based on the number of non-banking apps targeted out of the 29 analyzed by the zLabs team in 2023.
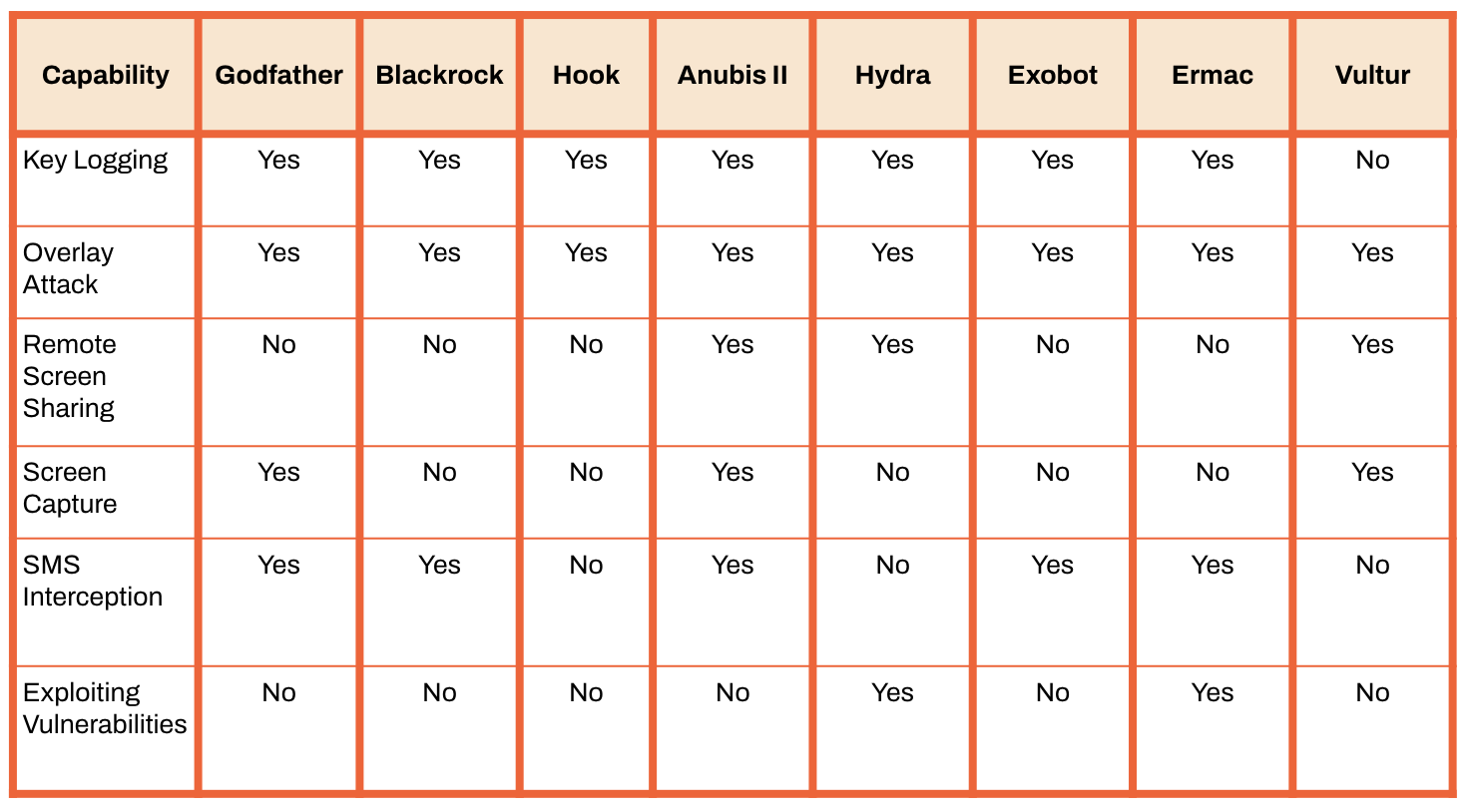
What key capabilities do these malware have?
The following is a list of key malware capabilities that enable theft and fraud on the device from the mobile app itself.
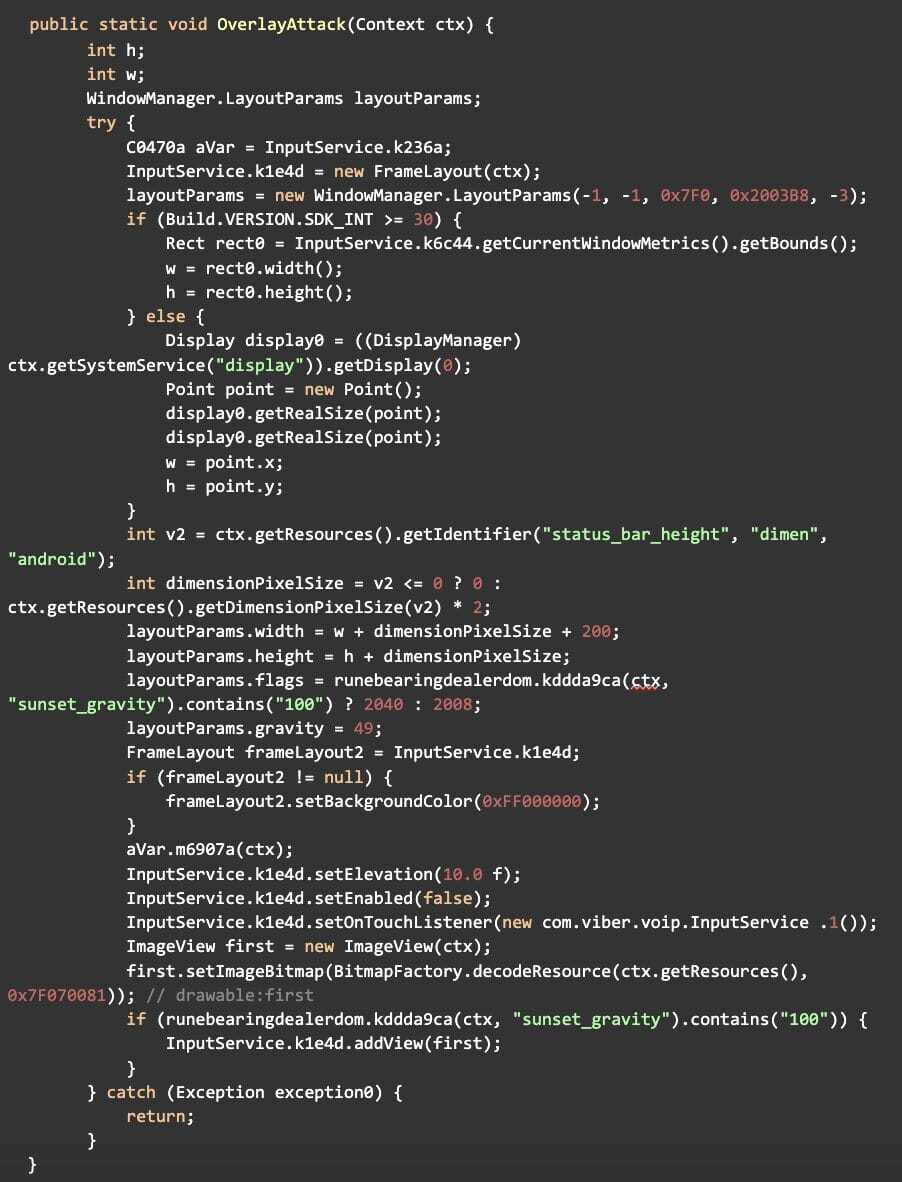
Here are some real-world examples of how these capabilities manifest within this malware.
- Below is a code snippet showcasing the “Overlay Attack” within the GodFather malware.
- Below is a phishing screens used in the targeting process.
What traditional security mechanisms are being undermined?
Let’s look at which traditional security mechanisms are being undermined by the Malware techniques mentioned above.
- Authentication Mechanisms: Through keylogging or overlay attacks, malware can intercept authentication credentials, bypassing traditional authentication mechanisms like passwords and biometrics.
- Data Encryption: Malware can encrypt sensitive data stored within the app, making it unusable to legitimate users.
- Secure Network Communication: Malware can intercept network communications, compromising the confidentiality and integrity of sensitive information transmitted between apps and remote servers.
- Code Obfuscation and Tamper Detection: Malware can tamper with code and behavior, bypassing tamper detection mechanisms and reverse engineering protections.
- Device Integrity Verification: Malware can exploit vulnerabilities to gain root access or escalate privileges, undermining mechanisms designed to detect and prevent unauthorized modifications to operating systems and devices.
Key Takeaways
- You aren’t a bank, but you are a target.
- It is important for brands not to assume that their mobile apps are not a target because they do not provide attackers direct access to funds. Apps that combine commerce, collaboration, and communication process a substantial amount of credentials, personal information, payment information, and enterprise secrets, all of which can be easily monetized.
- Your apps operate outside your enterprise perimeter.
- A pivotal realization for mobile application security and development leaders is that once an app is released into the wild, it is beyond the enterprise’s perimeter and control. It resides on app stores and devices, each representing a unique set of risks requiring specific security measures. End-user behavior further complicates this picture, as individuals’ phone use can introduce additional risks. Since most apps are easy to reverse engineer, malware authors also know which apps have no runtime visibility or protection.
- Insufficient traditional security measures invite trouble.
- Code sharing and Malware-as-a-Service models are becoming increasingly popular in the malware world. Malware actors developed LokiBot as ransomware malware, which asks users to pay in BTC, costing around $70-$100. Hydra was rented and marketed by threat actors on various online forums, with the cost being around $1500 – $2000. As a result, traditional security is rapidly being undermined by all malware, and more malware families will target your enterprise’s mobile apps.
How Zimperium can help
Today, Zimperium enables over 135 global financial companies to realize the full potential of mobile-powered business by activating a Mobile-First Security Strategy. Here are two solutions that directly help businesses build effective malware defenses for their mobile applications:
Advanced Application Shielding with Zimperium zShield
Zimperium zShield is an advanced code protection solution that provides robust protection against reverse engineering and app tampering techniques. The solution prevents threat actors from reversing the mobile banking app’s code and finding ways to abuse it, even with sophisticated tooling. Additionally, the solution prevents threat actors from repackaging legitimate apps with malware and cloning legitimate apps to create highly effective trojans.
Mobile apps protected by zShield can do the following:
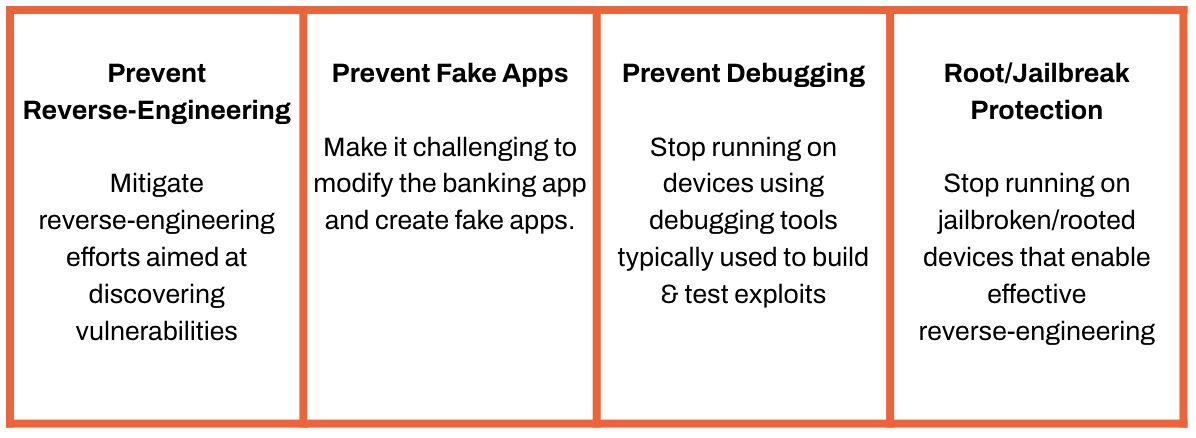
Learn more about zShield
With zShield, mobile app teams can create a hostile environment for threat actors.
Comprehensive Runtime Visibility and Protection with Zimperium zDefend
Zimperium zDefend is an in-app security SDK that enables mobile banking applications to detect and proactively protect themselves by taking actions on the end user’s device, even without network connectivity. The SDK leverages Zimperium’s patented dynamic on-device detection engine, which lies at the core of its multi-layered approach to detecting known and Zero-Day threats. The SDK sends runtime threat intelligence and forensics to a centralized console, giving security operations teams real-time visibility into risks and threats across all end-user devices. On-device actions pre-configured within the mobile application enable proactive protection. These actions can be updated in real time via the centralized console often without publishing a new version, making it practical and scalable across large install bases.
Mobile apps powered by zDefend can do the following:
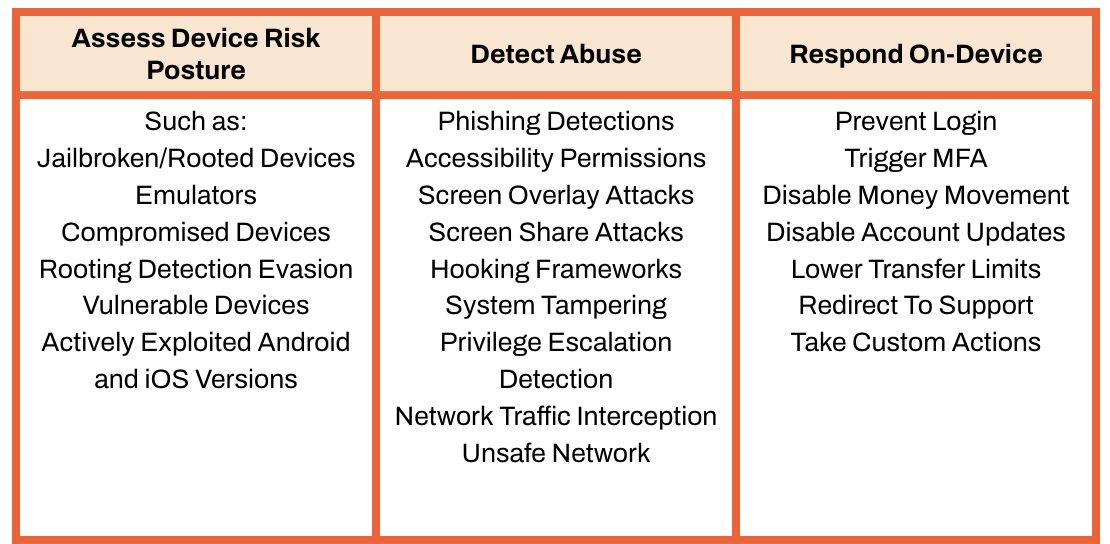
Learn more about zDefend
Zimperium’s ability to deliver comprehensive on-device runtime security without compromising the mobile experience is what sets it apart from alternative solutions in the market.
Conclusion
The evolving landscape of mobile malware, which targets a broad spectrum of applications beyond banking applications, calls for a fundamental shift in an organization’s approach to mobile app security.
The shift requires security and mobile application leaders to prioritize the development of resilient, self-defending applications capable of operating securely in inherently untrusted devices. This begins with protecting the application from being tampered with on app stores and end-user devices. Apps must be continuously assessed for vulnerability to abuse and proactively equipped to recognize untrusted environments to defend themselves and their data against bad actors, malicious tooling, and unauthorized activity. Malicious actors know that mobile apps are most vulnerable once they leave the enterprise perimeter.
By acknowledging the sophisticated and evolving nature of mobile malware and taking proactive steps to mitigate these threats, brands can protect their users and maintain the trust that is crucial to their success in the digital marketplace.