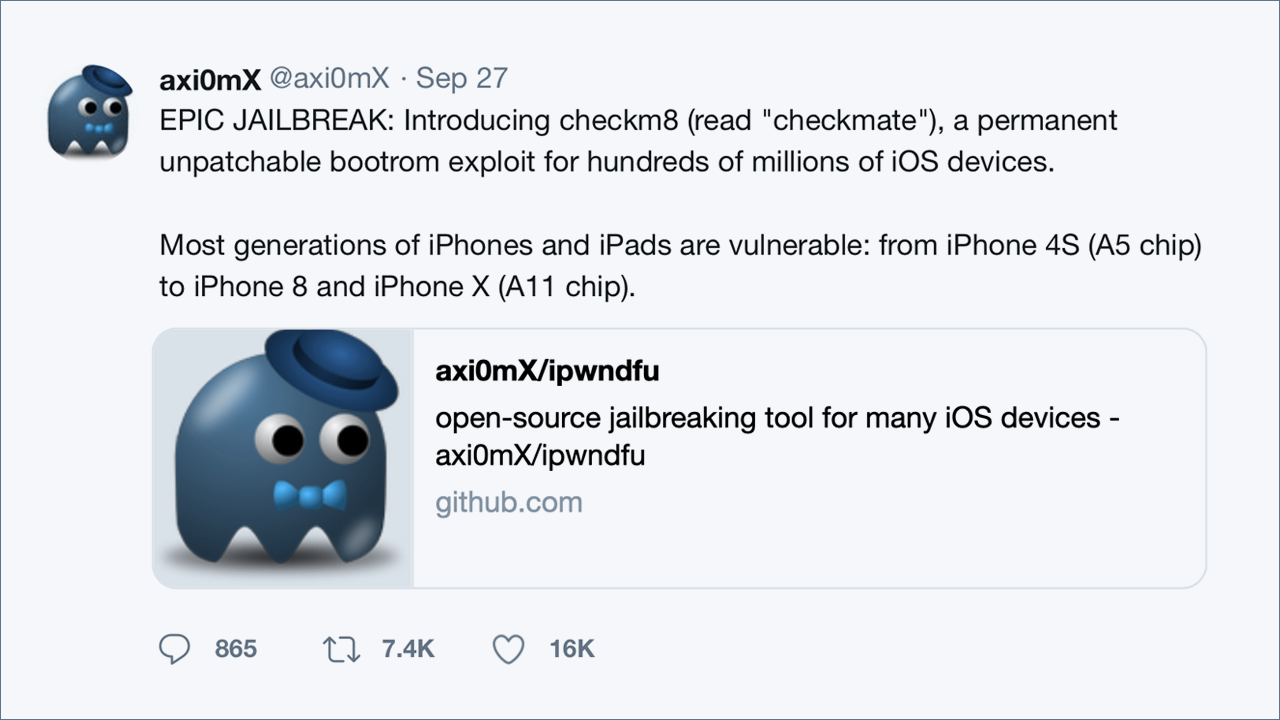
Can you explain what checkm8 is?
On Friday, September 27th 2019, a security researcher known as @axi0mX publicly disclosed a vulnerability together with a working exploit called checkm8 (read “checkmate”). This permanent and unpatchable exploit leverages a vulnerability in Apple’s bootrom (read-only code; SecureROM), the initial and critical part in the secure boot chain. Every stage in the boot chain cryptographically verifies the next one, starting with the SecureROM. When the SecureROM is exploited, the secure boot chain is then fully compromised, allowing additional code to load alternative code such as custom kernels or ramdisks.
Is checkm8 a Jailbreak?
Checkm8 is an exploit and not a jailbreak. It is in fact possible to leverage Checkm8 to load custom or modified kernels and support additional jailbreak capabilities or sideloaded apps, but so far this has not been publicly achieved. Since the exploit itself doesn’t persist across device reboots, persistence and other critical modifications would require additional vulnerabilities in iOS or its kernel.
What devices are affected?
Checkm8 does not discriminate on what device type or revision it can exploit (A5 and A11 chipsets). Below are the following iDevices impacted by checkm8:
- iPhone: iPhones starting with iPhone 4S (Apple’s A5 chip) and up to and including the iPhone X (Apple’s A11 chipset) are vulnerable. Apple XR through to the recent iPhone 11 are not affected as these devices are using Apple’s A12 and A13 chipsets, which do not contain the exploitable read-only code found in the bootrom.
- For newer devices that use Apple’s Secure Enclave, a user’s data is protected as a PIN is required to access the data on the device. (This is not the case for the older 32-bit devices like iPhone 4S, iPhone 5, or iPhone 5c which don’t have a secure enclave. For those, brute-forcing without restrictions is possible.)
- iPad: iPad devices starting with the iPad 2 (A5 SoC) up to the 2nd generation iPad Pro (A10X SoC), and just recently verified, the latest 10.2-inch iPad (A10 SoC).
- iPod: iPod touch models up to and including the most recent 7th generation devices.
- Apple TV: Apple TV up to Apple TV 4K
- Apple Watch: Apple Watch up to and including the Series 3 watch.
What is required to utilize this exploit?
To leverage the checkm8 exploit the following is required:
- Physical access to the device.
- The device needs to be put into DFU mode (Device Firmware Upgrade) – a configuration mode designed to perform firmware recovery of Apple devices. To enable DFU mode, a person must press a combination of hardware buttons on the device.
- A computer (PC / Mac) and a physical cable (ie. USB) connection. Checkm8 can NOT be triggered remotely or from the running operating system directly.
What is the significance and how could an attacker take advantage of this exploit?
A common objective of an attacker is to gain persistence to compromised systems to ensure ongoing control, data exfiltration and monitoring of the user, apps and device usage and associated data (i.e. SMS, instant messaging, files, etc.).
In order for an attacker to gain the necessary persistence while maintaining the secure boot chain intact, additional vulnerabilities would be required, for example, vulnerabilities to circumvent code signing for initial arbitrary code execution on boot.
Another, and the more likely attack surface for an attacker to gain persistence, is to replace legitimate apps (the device would need to be unlocked with the user’s passcode) with modified but legitimately signed apps that would provide a foothold on the device to allow data exfiltration or to perform other malicious actions.
Checkm8 alone is not a persistent exploit. If the device is rebooted, the device will need to be placed into DFU mode, and the checkm8 exploit will need to be executed each and every time to compromise the device.
How can Zimperium help assess and mitigate risk?
Checkm8 has the potential to provide a broad canvas for attack, compromise, and ongoing persistence of Apple devices. To evaluate risk posture of a device, it is important to leverage an MTD solution like Zimperium that can detect, respond and remediate threats in the following areas:
- Advanced Jailbreak detection
- Installation of a Vulnerable/Outdated OS for jailbreak purposes
- Suspicious Profile installation (used to access or install code outside of the Apple Appstore)
- Detection of Sideloaded App(s)
- File System Modifications
- OS System exploitation
- Attempts to hide exploitation or manipulate installed applications