Speaker: JT Keating, Zimperium’s Vice President of Product Strategy
Real World Examples: Mobile Threats Detected at Law Firms
Speaker: JT Keating, Zimperium’s Vice President of Product Strategy
The Mobile Menace Most Wanted List: #1 OS Exploits
Speaker: JT Keating, Zimperium’s Vice President of Product Strategy
The Mobile Menace Most Wanted List: #2 Rogue Profile
Speaker: JT Keating, Zimperium’s Vice President of Product Strategy
The Mobile Menace Most Wanted List: #3 Phishing
Speaker: JT Keating, Zimperium’s Vice President of Product Strategy
The Mobile Menace Most Wanted List: #4 Bad WiFi
Speaker: JT Keating, Zimperium’s Vice President of Product Strategy
“Mobile Devices Are The Single Biggest Hole In Security” | Why One of World’s Largest Energy Companies Is Implementing Mobile Threat Defense
Speaker: JT Keating, Zimperium’s Vice President of Product Strategy
The Mobile Menace Most Wanted List: #5 MITM
Speaker: JT Keating, Zimperium’s Vice President of Product Strategy
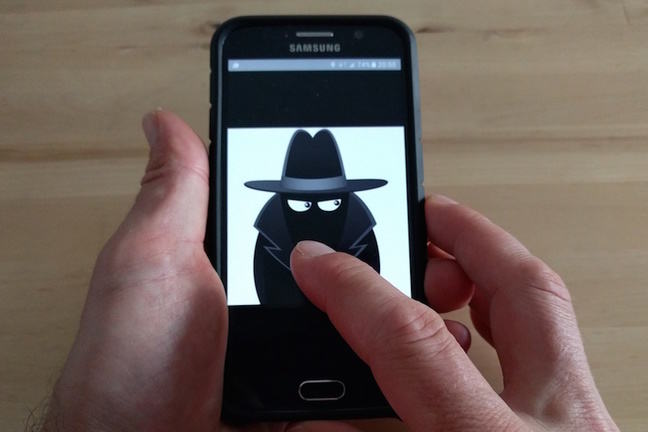
The Mobile Menace Most Wanted List: #6 Malicious App
Speaker: JT Keating, Zimperium’s Vice President of Product Strategy
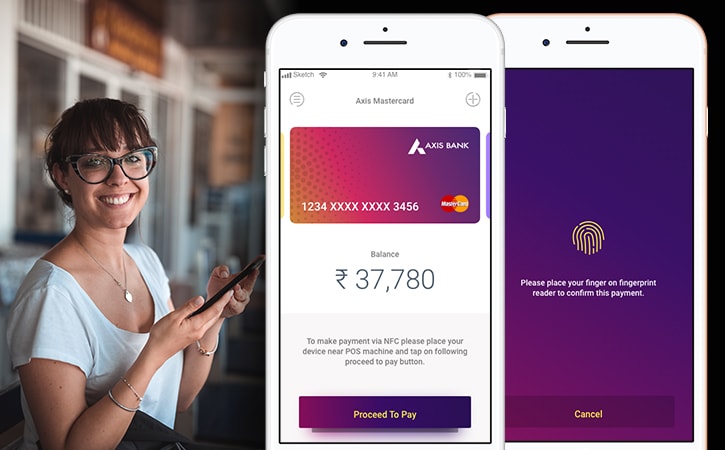
The Mobile Menace Most Wanted List: #7 Risky App
Speaker: JT Keating, Zimperium’s Vice President of Product Strategy
Categories
- Analyst Reports 11
- Case Studies 12
- Data Sheets 2
- Infographics 20
- News 316
- Press Releases 85
- Resources 40
- Solution Briefs 29
- Videos 16
- Webinars 152
- Whitepapers 59